SailPoint vs. Veza
See why SailPoint delivers true governance and control, not just visibility.
Why SailPoint?
Go beyond visibility with complete, automated governance
Identity security demands more than visibility. It also requires the ability to control and remediate access at scale. SailPoint delivers comprehensive governance through deep connectivity, automated workflows, and AI-driven intelligence. Veza’s limited remediation leaves critical governance gaps organizations cannot afford.
Do more with fewer resources
Cut costs while achieving more, see how we make it possible.
reduction in IAM team resources1
Boost efficiency instantly
Save time and reduce delays with streamlined onboarding.
decrease in new hire onboarding time2
Scale like never before
Handle more requests effortlessly with enhanced throughput.
increase in processing capacity3
At-a-glance comparison
SailPoint vs. Veza
Connector coverage and depth

250+ out-of-the-box, bi-directional connectors built for entitlement control
SailPoint provides hundreds of out-of-the-box, bi-directional connectors enabling deep entitlement visibility and control across SaaS, cloud, and on-premises environments. A flexible connector framework and community-built connectors extend governance to virtually any system type.
Veza
Full lifecycle management available for only a fraction of integrations
Veza offers full lifecycle management for only a small fraction of its integrations, with many connections limited to basic account provisioning. This can force organizations to rely on manual workflows or build custom governance capabilities, creating ongoing time and cost burdens.
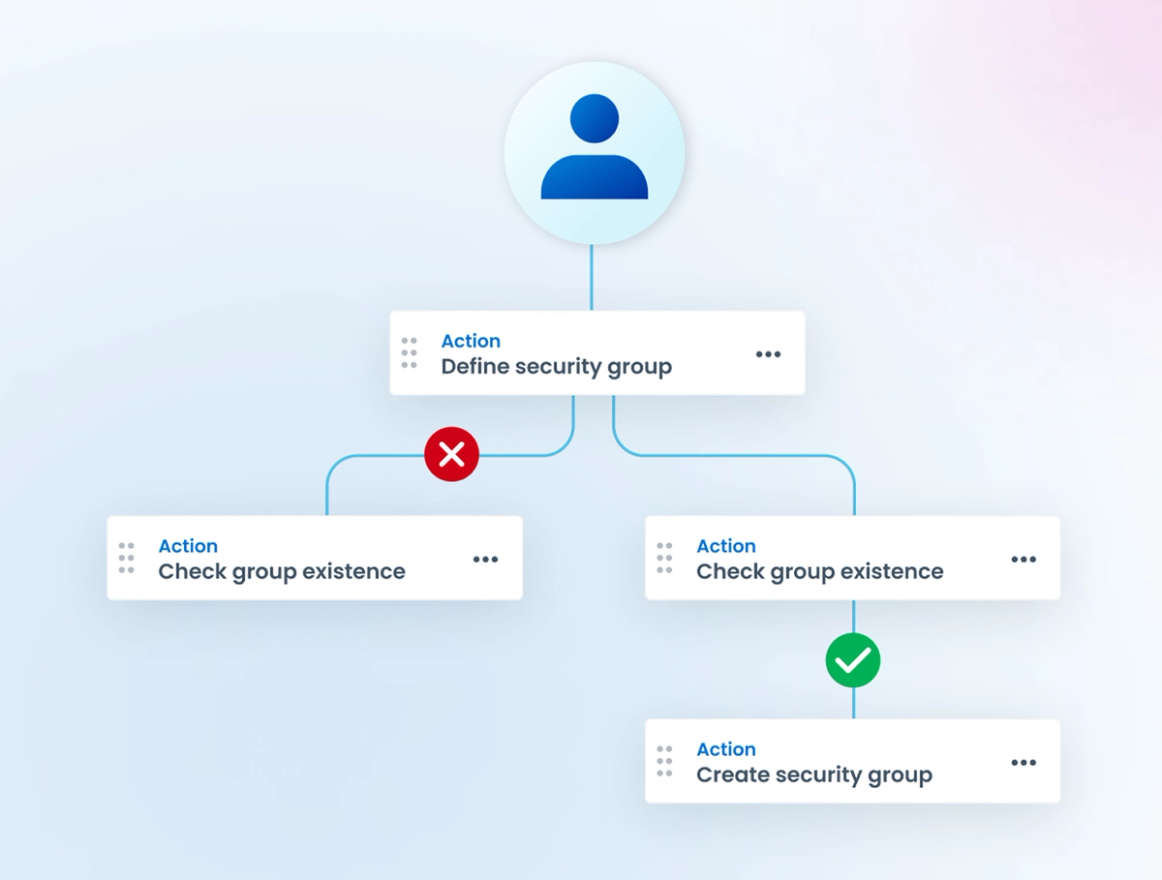
Identity governance automation

Automated, closed-loop remediation across all human and non-human identities
SailPoint delivers mature governance workflows including access requests, certifications, lifecycle management, and policy enforcement. Combined with built-in AI and ML intelligence, it closes the loop between identifying risky access and remediating it across all identity types.
Veza
Visibility-first approach limits automated, closed-loop remediation at scale
Veza focuses primarily on access visibility with limited entitlement management and automation support. Its reliance on scheduled, user-defined queries rather than proactive policy enforcement makes it harder to consistently operationalize risk reduction across the enterprise at scale.
Identity correlation depth

A robust identity model delivers full context and enables smarter governance
SailPoint builds a comprehensive, unified view of every identity including their fine-grained entitlements and associated access risks. This enables accurate policy decisions, intelligent automation, and consistent governance across all identity types and enterprise applications.
Veza
Simple email matching creates gaps in identity context and governance
Veza relies on basic email matching to correlate identities, which can result in a fragmented or incomplete view of user access. This limits the ability to make fully informed decisions and enforce intelligent, context-aware governance policies consistently across the enterprise.
AI and ML intelligence

Built-in AI and ML enable proactive risk detection and smarter governance
SailPoint embeds AI and ML throughout the platform with capabilities including access recommendations, identity outlier detection, role mining, and certification reviews. Harbor Pilot, SailPoint’s suite of AI agents enables agentic assistance across identity governance functions, from workflow creation to information discovery and access requests.
Veza
Query-driven intelligence limits proactive governance and automation
Veza emphasizes user-defined queries and scheduled reporting over proactive AI-driven governance. This reactive approach places more analytical burden on internal teams, reducing the platform’s ability to automatically surface and act on access risk without significant manual intervention.
Proven scale and experience

Thousands of customers, partners, and significant R&D investment worldwide
SailPoint serves thousands of customers globally, backed by hundreds of dedicated support staff, an extensive partner ecosystem, and consistent R&D investment. This depth of experience and resources ensures customers receive proven, reliable support for their end-to-end identity security programs.
Veza
Limited scale and resources for end-to-end identity security support
With approximately 150 customers globally, Veza has significantly less experience supporting complex, enterprise-scale identity security programs. More limited resources and a smaller partner ecosystem may make it harder to deliver the depth of support large organizations require.
Deeper comparison
See why leaders choose SailPoint

Full connectivity and control
Identity security means controlling access, not just seeing it. SailPoint’s 250+ bi-directional connectors, flexible connector framework, and Accelerated Application Management unlock fine-grained entitlement control across virtually any application. Veza’s focus on visibility means lifecycle management remains unsupported for the majority of its integrations.
- Gain bi-directional governance across 250+ out-of-the-box connectors, supplemented by extensive community-built options for any system.
- Onboard and govern new applications in days using AI App Onboarding and Accelerated Application Management.
- Eliminate costly manual workarounds with full out-of-the-box entitlement management and control across SaaS, cloud, and on-premises environments.
Closed-loop governance at scale
Finding risky access without removing it offers little real security value. SailPoint closes the loop with automated workflows for access requests, certifications, lifecycle management, and policy enforcement, all enhanced by built-in AI, ML intelligence, and the Harbor Pilot AI agent.
- Enforce access policy proactively with automated workflows that detect and remediate risky access consistently across the enterprise at scale.
- Leverage built-in AI and ML capabilities for smarter access recommendations, outlier detection, and faster certification decisions.
- Extend proven governance to agent and machine identities with Agent Identity Security and Machine Identity Security solutions.

Proven enterprise scale and identity security depth
As programs scale, niche tools struggle with enterprise complexity. SailPoint manages over 125 million identities and 5 billion entitlements on a modern, multi-tenant SaaS platform. Trusted by over half of the Fortune 500, SailPoint’s decades of R&D deliver a proven depth that Veza’s current scale cannot match.
- Manage over 125 million identities and 5 billion entitlements securely on a proven, modern, cloud-native SaaS platform.
- Benefit from decades of identity security R&D and proven enterprise expertise trusted by more than half of the Fortune 500.
- Partner with a vendor whose governance depth and enterprise capabilities are proven in production, not still being built toward maturity.
See SailPoint in action
Explore on your own
Take a self-guided tour of SailPoint's identity security platform
Take product tourStraight from our customers
What makes SailPoint their top choice?
Businesses worldwide trust SailPoint to empower their identity security. Here’s what they have to say.
"Sailpoint is the real gold standard for complex identity governance and administration."
"Some of the things that SailPoint’s solutions do now were things that we weren’t even thinking about five years ago. But now I can’t imagine not having a tool without those things. In a lot of cases, SailPoint operates behind the scenes without anybody knowing to get people the access they need to do their job as quickly as possible."

"Automates access reviews, suggests appropriate permissions using machine learning, identifies incompatible or suspicious access."
"We looked at SailPoint Identity Security Cloud as a potential tool and realised that it fits perfectly with ASDA’s new infrastructure and the future of where we’re heading. So far, integration has been straightforward – it’s gone really great."

"It’s an industry-recommended tool for any company that wants to control and manage its identity workflow effectively."
"Our employees have felt the operational efficiencies gained with the timely access they now have. Supervisors can actually see what their team has access to and review and approve it in one place. We’ve come a long way with SailPoint."

Related Resources
Keep exploring the value SailPoint delivers
Frequently asked questions
Common questions about SailPoint vs. Veza
What are the biggest advantages of the SailPoint Platform?
Govern all identities, human and non-human, from a single platform that delivers comprehensive visibility, automated control, and AI-driven intelligence.
What applications does SailPoint connect to and support?
SailPoint connects to hundreds of applications via 250+ out-of-the-box connectors, with community and custom options for virtually any system.
How quickly can organizations realize value from SailPoint?
AI App Onboarding and Accelerated Application Management enable comprehensive visibility and compliance for new applications in as few as days.
What AI and ML capabilities are built into SailPoint?
Capabilities include access recommendations, outlier detection, role mining, certification reviews, and the Harbor Pilot suite of natural language AI agents.
How does SailPoint secure non-human and AI agent identities?
Agent Identity Security and Machine Identity Security extend discovery, lifecycle management, and entitlement governance to agents and machines.
How does SailPoint support compliance and governance?
Built-in AI and automated workflows streamline access certifications, policy enforcement, and regulatory compliance reporting across the enterprise.
How does SailPoint compare to Veza on connector coverage?
SailPoint provides 250+ bi-directional connectors with full governance support, while Veza covers lifecycle management for only a fraction of integrations.
How does SailPoint’s identity model differ from Veza’s?
SailPoint builds a complete identity context view, while Veza’s email-based correlation limits governance accuracy and intelligent policy decisions.
- Anonymous digital infrastructure leader
Strengthen your defenses with adaptive identity
- Detect risk in real time. Continuously monitor identity behavior and surface threats the moment they appear.
- Adjust access dynamically. Automatically tighten or grant permissions based on risk, context, and user behavior.
- Protect every identity. Secure human, machine, and third-party access across your entire environment.