SailPoint vs. Okta Identity Governance
Compare outcomes. See why SailPoint is the governance standard.
Why SailPoint?
The governance platform built to scale with your enterprise
Identity governance is a distinct discipline, and SailPoint has spent over 20 years building exclusively for it. Where authentication-first platforms like Okta have added governance as an extension, SailPoint has built a platform where governance is the core, not the add-on, across over 3,000 enterprise deployments and counting.
Seamless high-volume offboarding
Easily handle large surges in temporary workforce transitions.
spike in offboarding seasonal employees, handled flawlessly1
Automate onboarding
Grant access instantly and eliminate manual effort.
automated provisioning for new employees2
The choice of industry leaders
Secure your workforce with the platform top companies choose.
of the Fortune 500 are SailPoint customers3
At-a-glance comparison
SailPoint vs. Okta Identity Governance
Governance depth

Purpose-built identity governance for 20+ years
SailPoint was built exclusively for identity governance from day one. Every capability, every connector, and every AI-driven workflow is engineered to answer the question enterprises cannot afford to get wrong: who has access to what, why they have it, and whether it still belongs.
Okta
Governance added onto an authentication platform
Okta's identity governance offering was introduced only in recent years as an extension of its core authentication platform. For organizations where compliance, SoD enforcement, and entitlement-level visibility are non-negotiable, a bolted-on governance layer introduces material program risk.
Connector coverage

250+ governance-enabled connectors, built and maintained natively
SailPoint's 250+ bi-directional connectors are all governance-enabled, covering cloud, legacy, and hybrid systems with real-time synchronization and closed-loop remediation. Every connector is built and maintained natively, with no dependency on third-party licensing or custom integration builds.
Okta
Connector breadth that rarely reaches entitlement depth
Only a fraction of Okta's connectors support entitlement management, and even those are typically limited to roles alone. Without visibility into groups and objects, governance gaps widen as entitlements evolve, leaving an increasingly inaccurate picture of who has access to what.
AI and automation

AI embedded in governance, where risk decisions are made
SailPoint's AI is built into the governance engine, delivering access modeling, peer-group recommendations, outlier detection, and certification suggestions without custom configuration. Harbor Pilot extends this further, letting teams query identity data and build workflows in natural language.
Okta
AI built for authentication, not governance decisions
Okta's AI investment centers on post-authentication risk scoring at the access layer. Governance automation depends on Okta's workflow engine, requiring ongoing technical configuration as business needs evolve, an IT burden that compounds rather than shrinks with program maturity.
Total cost of ownership

Comprehensive governance included out-of-the-box
SailPoint's base suites deliver extensive governance capabilities without dependency on third-party connectors, additional workflow licensing tiers, or custom integration maintenance. The cost model is transparent and designed to scale without compounding add-on fees as program scope grows.
Okta
Hidden costs compound as governance requirements grow
Okta Identity Governance is an add-on to the required Workforce Identity suite. Workflow automation requires its own licensing tier, and applications outside Okta's limited governance-capable connectors require third-party solutions, each carrying additional per-connector fees and IT maintenance costs.
Deeper comparison
See why leaders choose SailPoint
Governance depth, not just reach
Integration count alone does not equal governance. Where Okta offers a broad integration library with limited entitlement support, SailPoint's connectors are all governance-enabled natively, covering cloud, legacy, and hybrid systems without third-party dependencies or custom builds.
- See not just who has access, but exactly what they can do inside every connected application.
- Eliminate third-party connector dependencies and the licensing costs that come with them.
- Maintain real-time synchronization and closed-loop remediation across your entire application landscape.
Built to scale without compromise
When an entitlement changes inside a sensitive application, your governance platform needs to see it, act on it, and close the loop automatically. That requires a connector built for governance, not just provisioning. SailPoint's native connector architecture ensures that as user entitlements evolve, the answer to who has access to what stays accurate, current, and audit-ready across every connected system.
- Catch entitlement drift before it becomes a compliance finding with real-time synchronization across all connected systems.
- Govern access inside applications, not just to them, with full entitlement visibility down to the permission level.
- Extend governance to unstructured data, cloud infrastructure, and non-human identities from a single native platform.

AI built for governance, not just authentication
Authentication intelligence tells you something looks suspicious after access has already been granted. Governance intelligence prevents the wrong access from existing in the first place. SailPoint's AI operates at the decision layer, informing who should have access, flagging what looks anomalous, and streamlining the certification process so governance programs run continuously rather than reactively.
- Shift from reactive access reviews to continuous, AI-informed governance that surfaces risk before auditors do.
- Make smarter provisioning decisions with role recommendations built from real access patterns across your organization.
- Put governance in reach of every stakeholder, not just IT, with natural language workflows through Harbor Pilot.
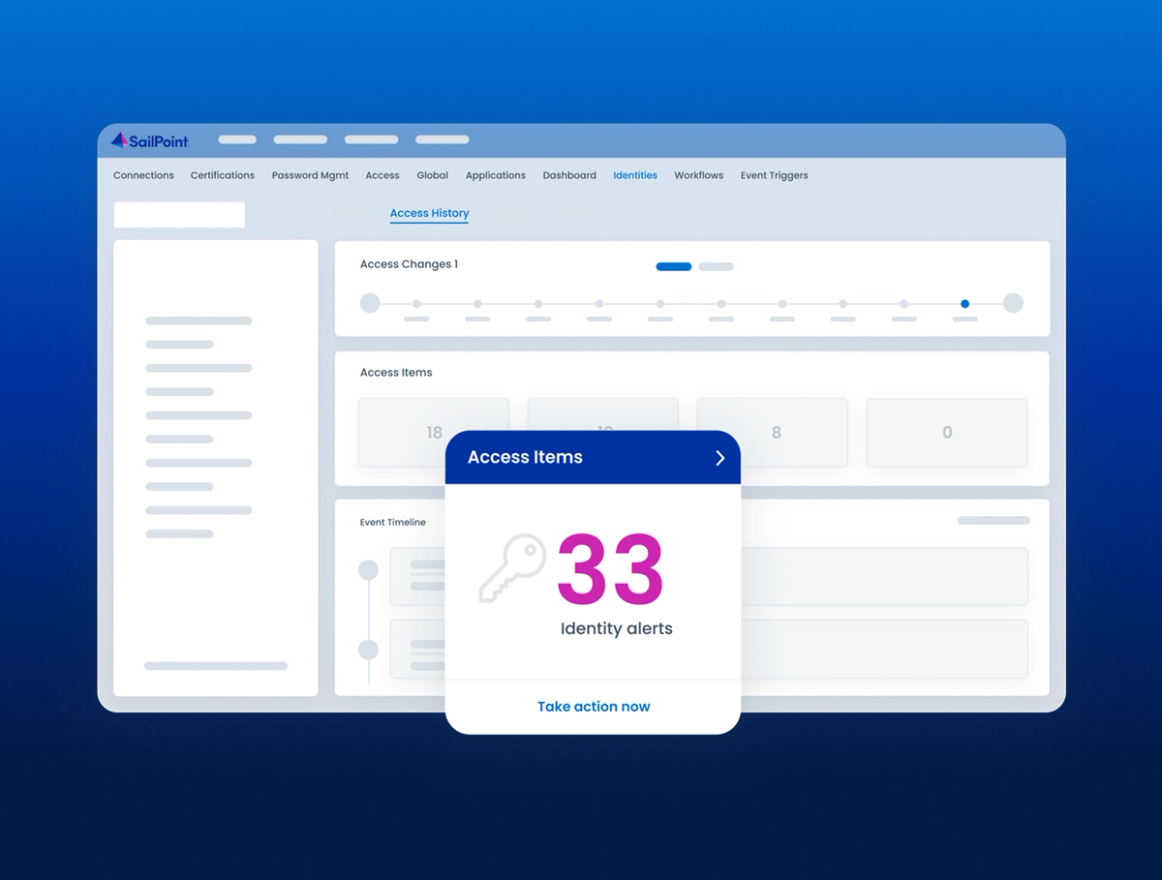
See SailPoint in action
Explore on your own
Take a self-guided tour of SailPoint's identity security platform
Take product tourStraight from our customers
What makes SailPoint their top choice?
Businesses worldwide trust SailPoint to empower their identity security. Here’s what they have to say.
“The platform approach of SailPoint is impressive, particularly in how it is continually bringing in more capabilities for future identity feature sets. I find this continuous improvement promising.”
“The SailPoint platform has allowed us to initiate our identity and access governance programme with speed and efficiency.”

“What I really appreciate is how simple the workflow is. I can always see exactly where a request is stuck, which means I know who to approach next without guessing. It saves us all a lot of time.”
"We had limited time and strict parameters, yet we successfully carried out this identity security project in record time and with a ‘One-Team’ spirit."

“SailPoint has allowed our team to transform the way identity management operates within our company.”
“My end goal is to make every identity a privileged identity, whether it's human or machine. And we see the potential to achieve this on the SailPoint platform."

Related Resources
Keep exploring the value SailPoint delivers
Frequently asked questions
Common questions about SailPoint vs. Okta Identity Governance
Can SailPoint and Okta be used together?
Yes. Many enterprises run Okta for authentication and SailPoint for governance. The co-existence model is the industry norm at Fortune 500 scale.
How does SailPoint's connector coverage compare to Okta?
SailPoint offers 250+ governance-enabled connectors. Okta's library, while broad, includes only a fraction of connectors that support entitlement management, leaving most applications ungoverned.
What makes SailPoint better suited for compliance programs?
SailPoint delivers entitlement-level visibility, automated SoD enforcement, and continuous audit trails purpose-built for SOX, HIPAA, and GDPR requirements from day one.
How does SailPoint handle non-human and machine identities?
SailPoint delivers production-ready machine identity security, non-employee risk management, and cloud infrastructure entitlement management today.
What AI capabilities does SailPoint offer for governance?
SailPoint embeds AI into the governance engine, delivering access modeling, outlier detection, certification recommendations, and Harbor Pilot workflows.
Contact us
Strengthen your defenses with adaptive identity
- Detect risk in real time. Continuously monitor identity behavior and surface threats the moment they appear.
- Adjust access dynamically. Automatically tighten or grant permissions based on risk, context, and user behavior.
- Protect every identity. Secure human, machine, and third-party access across your entire environment.