Blog
Beyond the graph: Using identity intelligence to close the exposure gap
In identity security, the real threat isn’t a single, obvious vulnerability. It’s the quiet, relentless accumulation of stale permissions, nested groups, and over-privileged accounts. The challenge for practitioners isn't just seeing these risks; it’s finding the signal in the noise before exposure leads to a security incident.
Since introducing SailPoint Observability & Insights at Navigate 2025, we’ve provided the visual map of your identity landscape. Now, we’re transforming that map into an active control plane. Our Q1 2026 enhancements turn visibility into active intelligence, allowing you to identify, contextualize, and remediate risks across human, machine, and AI identities from a single, unified view.
What's new: Connecting identity, data, and action
This launch brings a new level of intelligence to the Identity Security Cloud, specifically enhancing Observability & Insights with the deep data access context of SailPoint Data Access Security. This unifies identity context and granular data access into a single, powerful view for managing sensitive data exposure.
- Deep data access visibility: Reveals the end-to-end access pathway from any identity to sensitive, business critical, or regulated data.
- Prioritization with data classification: See which access paths pose the most risk by visualizing data sensitivity directly in the graph.
- Proactive insights surfaced in the graph: Automatically flag high-risk hygiene issues, such as dormant accounts and partially offboarded accounts, for immediate review and remediation.
- Direct in-graph actions: Revoke risky entitlements or de-provision accounts with a single click, directly in the graph view where the risk is found.
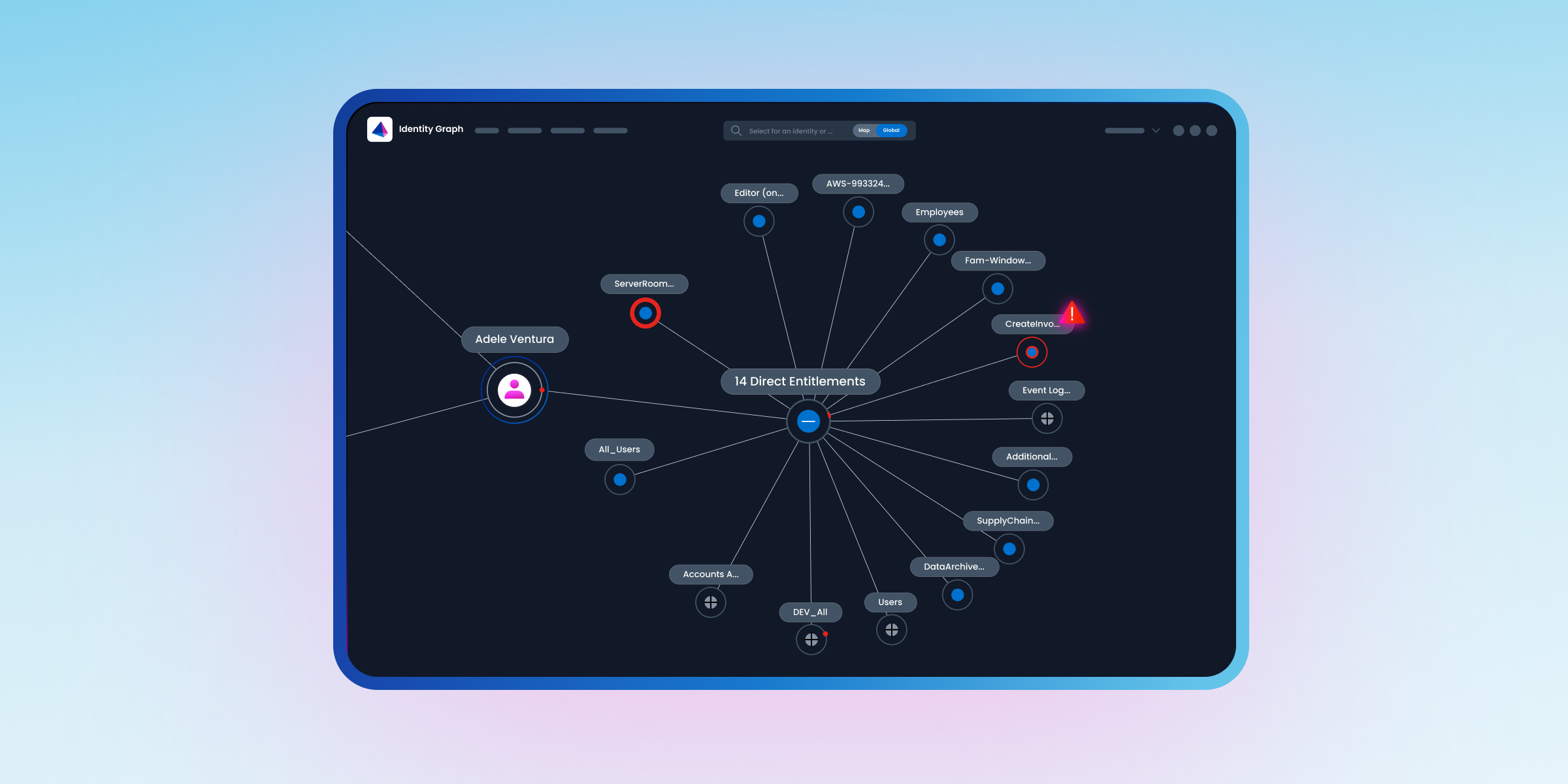
Go beyond knowing who has access to understanding how. Observability & Insights provides the relational context needed to see the full, end-to-end access chain.
Visibility: Illuminating the path to sensitive data
For too long, identity security focused on who had access, leaving the critical question of "access to what?" unanswered—especially in the sprawling world of unstructured data. We are closing that gap. With Data Access Security now enhancing Observability & Insights, the SailPoint Identity Graph is enriched with vital data context. It no longer just shows that an engineer has access to a SharePoint site; it reveals the direct and indirect pathways from human, machine, or AI agent identities to sensitive information.
This capability is unique to the Identity Graph, which can unravel the complex web of nested group memberships and indirect permissions that create unintended access routes—the kind of hidden access that audits and spreadsheet reports simply cannot find. You can finally see the complete, end-to-end chain from identity to data.
Intelligence: Prioritizing risk and reducing exposure
Visibility tells you where the roads lead, but identity intelligence tells you which ones pose the greatest risk. In a sprawling digital ecosystem, security practitioners need a way to filter the noise and pinpoint the "live wires"—the identities that represent the most significant potential for exposure.
With this release, we’ve introduced powerful new intelligence and hygiene capabilities to do just that:
- Focus on high-impact access: Instantly identify the access pathways that could have the biggest impact on your organization. Filtering your visualization by data sensitivity (high, medium, low), lets you prioritize reviews on privileged entitlements protecting your most critical business data.
- Surface risky accounts: Automatically flag identities like dormant and partially offboarded accounts that still hold pathways to data. Instantly spot the released contractor or the role-changer who still maintains legacy access.
- Validate for anomalies: Use side-by-side comparisons against a “known-good” baseline to spot privilege creep or anomalous access before it becomes a liability.
This is how you move from asking "What happened?" to knowing "What is out of alignment right now?"
Action: Closing the loop with direct remediation
Visibility provides intelligence; control delivers the security. Historically, remediating a risk meant pivoting to other tools, filing tickets, and waiting—all while the window of exposure remained open. We have closed that gap. With direct remediation now embedded in the Identity Graph, you can act on intelligence the moment you find it.
With a few clicks, you can perform precision pruning and transform a slow investigation into a decisive security action, such as:
- Revoking specific, high-risk access.
- De-provisioning an orphaned or dormant account entirely.
By connecting insight directly to action in a single view, you dramatically shorten the time from detection to remediation, ensuring that finding a risk is the same as solving it.
Outcome: A hardened, audit-ready perimeter
What does this unified workflow look like in practice?
During a routine security check, a security analyst reviews the Identity Graph, where built-in data classifications immediately highlight the most critical access paths. This allows them to instantly spot a dormant service account with inherited access to a folder containing "Crown Jewel" M&A documents. With a single click, they revoke the risky entitlement on the spot.
This is the systematic reduction of the blast radius, performed as proactive, daily hygiene. It moves the organization away from frantic, post-breach cleanup and toward a hardened security posture. The result is a state of continuous audit-readiness, where compliance becomes the natural byproduct of strong identity-centric security practices.
From seeing to solving
This level of proactive defense is only possible on a unified platform. The SailPoint Identity Security Cloud was architected to natively link the context of identity with the reality of data access, putting identity at the core of your security strategy.
By evolving Observability & Insights into an actionable control plane, we are empowering you to stop just seeing risk and start controlling it. This is the intelligence, speed, and precision that modern identity security demands.
Ready to move from seeing risk to solving it? See how unifying identity and data provides the intelligence and control a modern security posture demands. Request a demo to see it in action.
