Extensibility
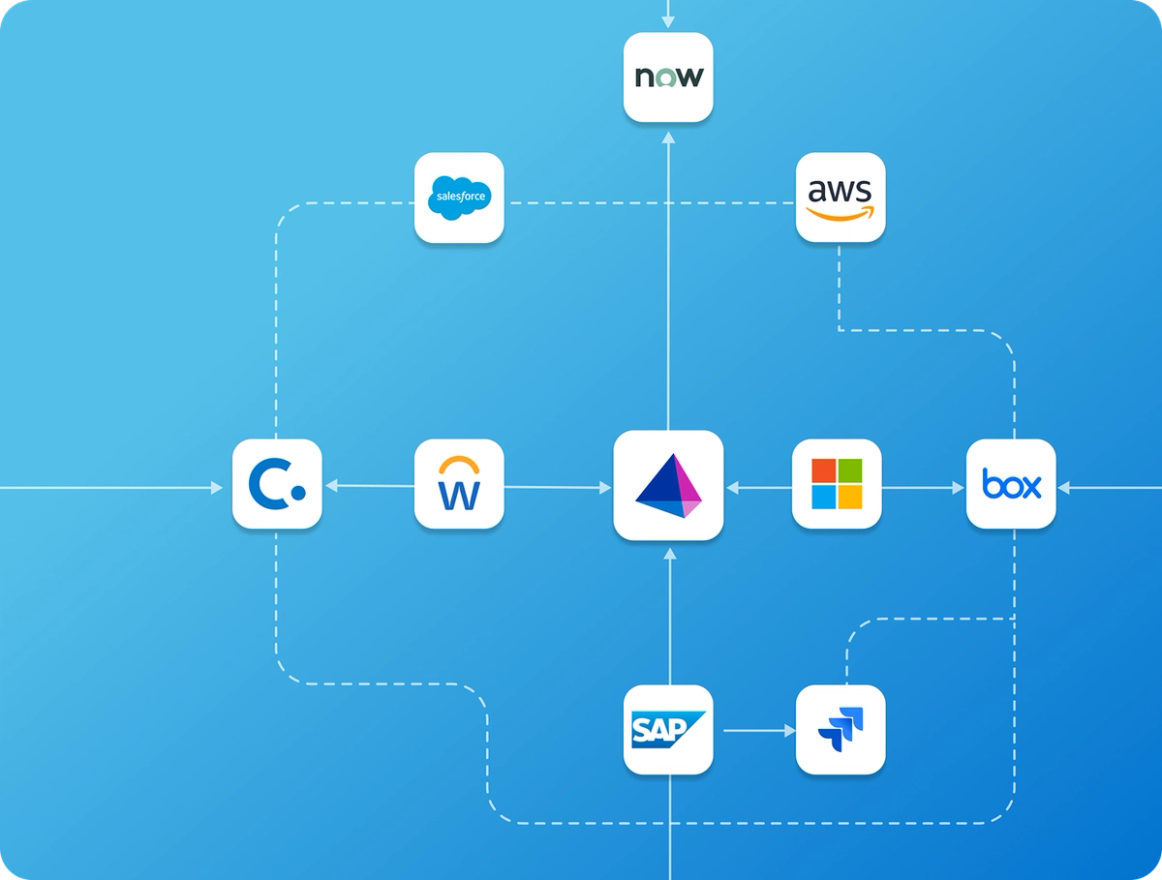
Seamless identity security across systems
Extend identity security across HR, ITSM, IaaS, and SIEM via APIs and event triggers.
Challenge & solution
Rigid identity platforms limit scale
Identity teams struggle to extend governance beyond out-of-the-box integrations. Custom needs require scripts, point solutions, or manual work, creating brittle processes, slow response to change, and gaps between identity, security, and business systems.
Extend identity security everywhere with:
Open APIs and event-driven architecture for seamless integration.
Low-code workflows to extend identity processes without scripts.
Real-time signals from security and business systems.
Scalable extensibility across all identity types.
Custom actions and logic tailored to enterprise needs.
Use cases
Extend protection across your identity fabric
Extensibility lets organizations embed identity security into the systems and processes they rely on. Using APIs, events, and workflows, teams can integrate identity context across IT, security, and business tools to automate actions, reduce risk, and scale securely.
Customize how you use our APIs and event triggers
Leverage SailPoint APIs and event triggers to tailor identity governance with your unique business processes. Integrate seamlessly with existing systems, automate lifecycle actions, and respond to identity events in real time. By tailoring API calls and trigger-based workflows, teams can extend SailPoint Identity Security Cloud functionality, reduce manual effort, and ensure faster, more accurate identity decisions across the enterprise.
Seamlessly connect AI agents with identity security
AI-ready interface that modernizes access management by securely connecting AI applications to SailPoint Identity Security Cloud through the SailPoint Model Context Protocol (MCP). It acts as a standardized bridge that allows AI-powered agents to request, manage, and act on access in a governed way, translating agent actions into identity-aware commands the platform understands. It embeds identity controls directly into AI interactions to help boost productivity, reduce IT workload, and ensure access decisions remain secure, auditable, and aligned with identity governance policies.

Fuse identity and security context with real-time shared signals
Bring native support for real-time identity and security signal exchange into SailPoint Identity Security Cloud, eliminating the complexity of manual setup. Seamlessly receive signals from tools like XDR, SIEM, SOAR, ITDR, and device management systems to enable dynamic security orchestration powered by SaaS Workflows. Transforms identity from a static gatekeeper into a risk-aware responsive layer of enterprise defense, continuously adapting access based on live security intelligence.
Related resources
Learn more about Extensibility
SailPoint Atlas Enterprise overview
Learn how SailPoint Atlas Enterprise provides you the flexibility to move beyond basic automation, make informed decisions, streamline operations, and enhance collaboration by fusing identity and security data and delivering the precise insights your stakeholders need.
Start your identity security journey today
SailPoint Identity Security Cloud empowers organizations to intelligently manage and secure real-time access to critical data and applications.
Advanced capabilities
Take your identity security solution even further
SailPoint defines the future of adaptive identity for the AI-driven enterprise. Our comprehensive vision and AI-powered platform empower you to secure every identity—human and non-human—transforming risk into a powerful advantage and enabling confident AI innovation.
faq
How extensibility works
Why is extensibility important for identity security?
Extensibility is essential to identity security because modern enterprises are constantly evolving across cloud, SaaS, and custom environments. An extensible identity platform ensures all users, applications, and data—no matter how unique—can be governed without gaps. It allows organizations to adapt quickly to new technologies, integrate with existing security and business systems, automate access controls at scale, and future-proof their identity strategy while maintaining strong visibility, compliance, and least-privilege access.
Does SailPoint provide open APIs?
Yes, SailPoint provides a comprehensive set of REST APIs designed for broad and flexible integration. These open APIs serve as the foundation of our extensibility framework, allowing your teams to seamlessly access identity data, trigger governance actions like access requests or certifications, and extend identity workflows to other platforms without requiring deep, complex customization. This API-first approach empowers developers to build custom solutions, connect to homegrown applications, and integrate identity processes into third-party tools, ensuring that your identity security platform can adapt to your unique business needs and technology landscape.
How does extensibility work with SailPoint workflows?
Extensibility supercharges SailPoint workflows by enabling them to interact with external systems and respond to events in real-time. Workflows, which are powerful no-code automation tools for orchestrating identity processes, can use extensibility to make API calls to outside platforms, such as creating a ticket in ServiceNow or posting a notification in Slack. Conversely, workflows can be triggered by events from external systems, like an alert from a security monitoring tool. This two-way communication allows you to orchestrate complex, cross-platform identity actions, such as automatically disabling access in response to a risk signal or provisioning resources based on an HR system update. This capability turns your identity platform into a central hub for automating and governing identity-related tasks across your entire enterprise.
Can extensibility support adaptive or risk-based automation?
Yes. Identity risk, access changes, and external signals can trigger automated, context-aware actions.
Does extensibility scale across all identity types?
Absolutely. Extensibility is a key enabler of adaptive, risk-based automation. By integrating with various data sources, SailPoint can ingest signals from your broader security environment, such as alerts from a SIEM or endpoint detection system. When a change in identity risk is detected, like a user accessing a sensitive system from an unusual location, it can automatically trigger a workflow. This workflow can then perform a context-aware action, such as initiating a multi-factor authentication step-up, requiring a manager to re-certify access, or even temporarily suspending an account. This ability to automate responses based on real-time risk signals allows you to move beyond static policies and create a dynamic security model that adapts to emerging threats.
Does SailPoint support event-driven integrations?
Yes, SailPoint fully supports event-driven integrations to enable real-time, adaptive identity security. Using its event-based architecture, APIs, and workflows, SailPoint can publish and consume events such as identity changes, access requests, risk score updates, lifecycle events, and external security signals. These events can automatically trigger workflows and orchestrated actions across connected systems—such as HR, ITSM, SIEM, XDR, ITDR, and cloud platforms—without manual intervention. This allows identity decisions and enforcement to happen as conditions change, rather than on static schedules, enabling faster response, consistent policy enforcement, and tighter alignment between identity governance and the broader security ecosystem.
Can organizations build custom extensions or logic?
Yes. Organizations can build custom extensions and logic with SailPoint to tailor identity security to their unique business, security, and technical requirements. Using open REST APIs, event triggers, low-code workflows, and custom actions, teams can integrate SailPoint with external systems, apply specific business rules, and orchestrate identity-driven actions across their ecosystem. This approach allows organizations to extend governance, automate responses, and embed identity context into existing processes without heavy customization or brittle scripting, while maintaining auditability, scalability, and centralized control.
Contact us
Put identity security at the core of securing your business


