Access management is a set of processes and practices used to restrict who or what (i.e., humans and non-humans) can use various resources, such as systems, applications, data, and networks. It includes defining, tracking, controlling, and managing authorized or specified users’ access to and usage of resources and preventing unauthorized access.
Access management encompasses all functions related to policy administration, authentication, and authorization, as well as defining user profiles and roles. Access management initiatives are often coordinated with data governance.
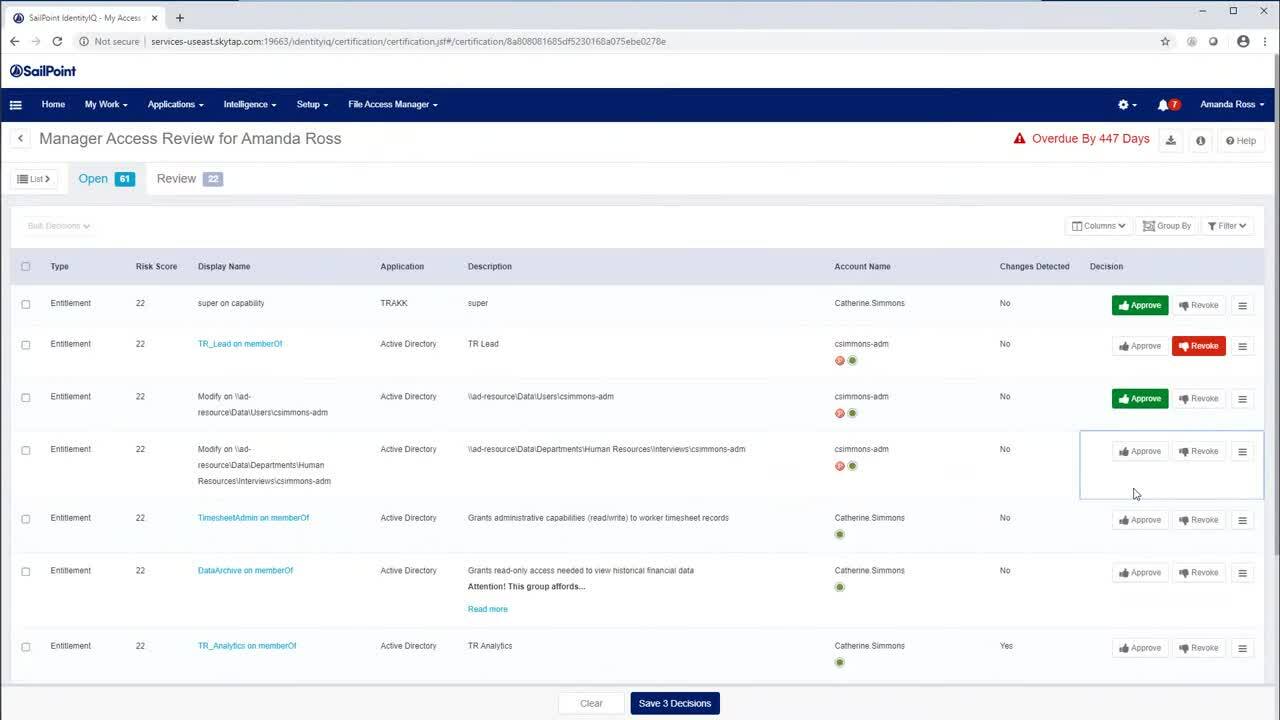
See how SailPoint's Recommendation Engine can help you decide whether access should be granted or removed and help your team make more informed access decisions with the power of AI.
The function of access management extends to the entire lifecycle of a user’s authorization period; it begins when a user is granted certain access privileges and ends when the user’s access is terminated.
Benefits of robust access management processes include:
- Tracking of all activities and login attempts (i.e., from both authorized and unauthorized users)
- Control over the allocation of permission to access resources
- Consistent provisioning and management of user access rights and privileges
- Structure for efficient onboarding and offboarding of users
Key terms used with access management include the following.
Access manager
Also referred to as the process owner, the access manager role is responsible for executing policies defined by the security team. This role also oversees the provisioning of authorized users (i.e., those given the right to use a service) and blocking access to non-authorized users.
Access rights
The set of data and services a user is authorized to use is referred to as access rights. Access rights are granted by assigning the user, identified by a user identity, to one or more user roles.
Privileged access management
Special access and capabilities are required for a limited number of IT administrators; controlling this is referred to as privileged access management (PAM). These accounts require strict access management as these users can see and control most systems.
Request for access rights
Part of the access management function is fielding requests to grant, change or revoke the right to use services or assets.
User identity record
When establishing access privileges, a user identity record provides details about a human or non-human user’s identity. This is used to determine the appropriate access privileges that should be granted.
User identity request
Access management also includes handling requests to create, modify or delete a user identity.
User role
In some organizations, access management includes creating a catalog of the different types of users and groups of users and what privileges each has and managing associated controls and rights.
Workforce access management vs customer access management
Workforce access management is meant to support organizations’ internal teams. It provides controls that allow employees to connect to internal applications and systems.
Following the principle of least privilege, workforce access management should only allow employees access rights based on minimum requirements to perform their jobs. Because employees can have access to sensitive information, a high degree of security should be in place, with user experience a close but definite second to security.
| Workforce access management | Customer access management |
|---|---|
| Authentication is usually performed using internal directory services | Authentication is usually performed with one-time passwords or social media |
| Can scale from tens to hundreds of thousands of user IDs | Must be able to scale to hundreds of millions of user IDs |
| Data usage and access are governed by corporate policies | Data usage and access are governed by a variety of global privacy and data protection regulations |
| Primarily manages employee identities for internal access | Manages consumer identities on consumer-facing sites across multiple channels (e.g., Internet of Things, mobile, and web) |
| Privileges govern access to internal IT systems or protected cloud environments from a closed, corporate network | Privileges provide access to customer-specific IT systems on public networks and connections |
| Profile data is collected for administrative and operational purposes | Profile data is collected to support usage as well as for marketing purposes and is often shared with third parties |
| Users are onboarded by human resources or IT teams who input profile data | Users register themselves and create their own profile data |
| User experience is secondary to security (i.e., users are expected to tolerate latency, cumbersome user interfaces (UX), and sometimes poor performance) | User experience is the primary objective, because customers have very low tolerance for latency, cumbersome user interfaces (UX), and poor performance |
Access management and multi-factor authentication
Multi-factor authentication (MFA) can be included in access management policies. Used as an extra layer of protection, MFA can enforce access management protocols to prevent unauthorized users from gaining access even if credentials have been compromised.
With multi-factor authentication, users must provide their credentials as well as at least one other form of identity verification. MFA requires users to provide one of three types of information in addition to their login credentials:
- Inherence
Things unique to the person, such as biometrics (e.g., fingerprints, retinal or iris scans, or voice recognition) or behavior - Knowledge
Things the user knows, such as the correct answer to a secret security question - Possession
Things only a legitimate user would have, such as an access badge, USB device, or smartphone
Access management and single sign-on
Single sign-on (SSO) is another access management tool for controlling access to applications and resources that reside within a single domain. With SSO, users can use one set of login credentials.
The single sign-on system authenticates the user and generates a certificate or token that acts as a security key for other resources. Systems use open protocols, such as Security Assertion Markup Language (SAML) or OAuth 2, to share keys freely between service providers.
SSO can be used as part of access management for any type of user (e.g., employees, customers, vendors, partners). A commonly cited benefit of single sign-on is that it provides a centralized user authentication service that eliminates the need for users to remember multiple usernames and passwords for different services.
Why businesses need access management
Access management can support an organization’s security posture, improving security and mitigating risk. It also:
- Allows external users (e.g., partners, vendors, and contractors) to access a corporate network without compromising security
- Automates, captures, records, and manages user identities and access permissions
- Facilitates compliance with industry regulations
- Governs all users under a standard policy to ensure proper authentication and authorization
- Improves security and mitigates risks from external hackers and insider threats
- Increases IT departments’ efficiency by eliminating many manual identity and access management processes
- Mitigates data breach risk by enforcing stronger user access control and the principle of least privilege
- Supports ongoing monitoring of identities and access points to identify suspicious behavior
Safeguarding data and systems with access management
Access management can play an important role in reducing overall security risk. Taking time to develop, manage, and implement access management controls can help organizations better protect critical systems and valuable data as well as enable compliance with evolving requirements.