ACCESS RISK MANAGEMENT
Manage and mitigate SAP access risk
Extend identity security to detect, prevent, and manage separation of duties (SoD) conflicts and sensitive access risk for SAP.
Challenge & solution
Control SAP access risk before it’s a compliance problem
Managing SoD risk for SAP ECC, S/4HANA, and Fiori applications is complex — especially with fragmented controls and manual reviews. SailPoint Access Risk Management streamlines GRC controls, enabling preventative SoD checks and risk analysis to reduce fraud, errors, and compliance violations across hybrid SAP landscapes.
How SailPoint Access Risk Management Helps
Unify risk management and SoD analysis for complex SAP landscapes
Identify, simulate, and prevent SoD conflicts before provisioning
Automate access reviews and emergency access workflows
Gain comprehensive visibility into utilization and sensitive transactions

Use cases
Streamline SAP SoD access controls
SailPoint Access Risk Management empowers organizations to uncover and control SoD access risk on SAP ECC, S/4HANA and Fiori applications that are hosted on-premises as well as on SAP RISE. Integrated with SailPoint Identity Security Cloud, it combines predictive risk analysis, real-time SoD monitoring, and automated controls to simplify audits, prevent fraud, and reduce operational overhead.
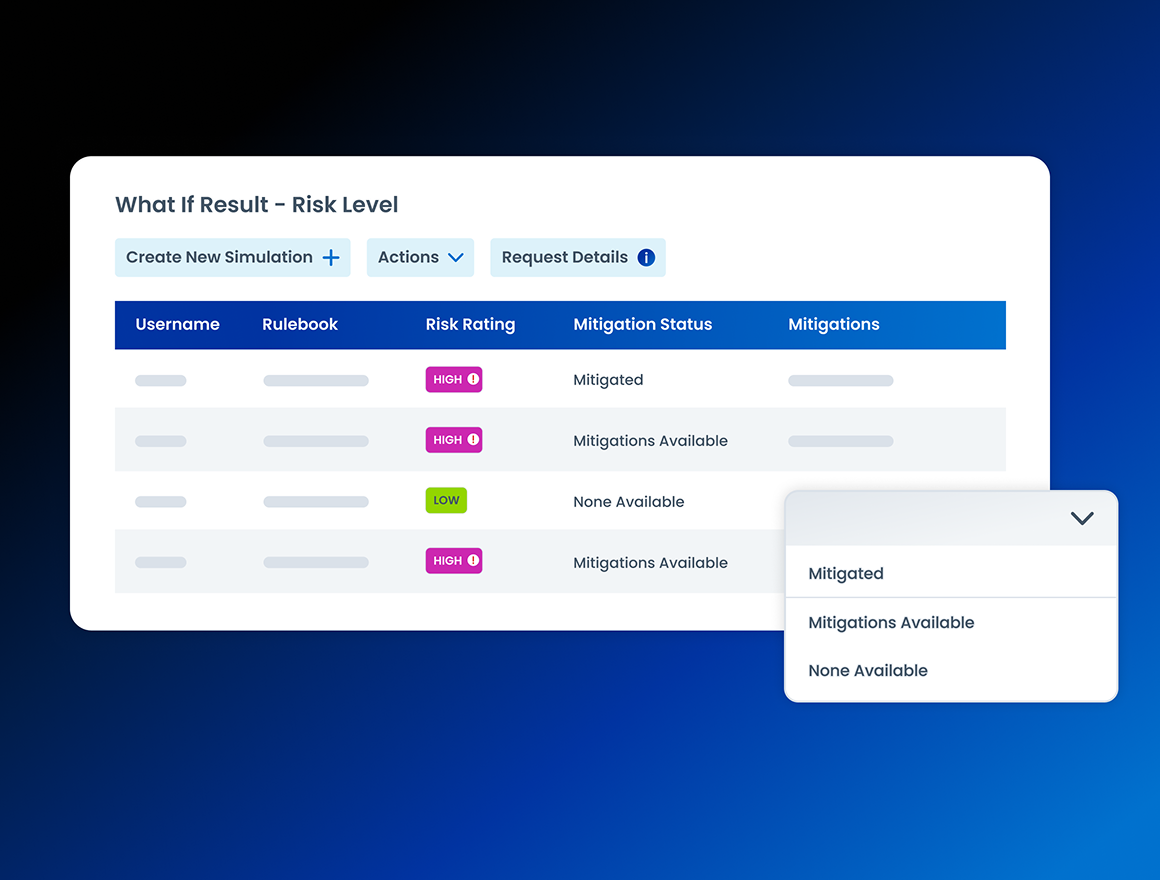
Prevent SoD conflicts before they happen
Simulate and analyze access changes before they’re applied to prevent violations and risky combinations of roles. With real-time modeling and automated policy enforcement, SailPoint Access Risk Management helps you maintain compliance and reduce costly audit remediation.
- Prevent SoD conflicts for SAP ECC, S/4HANA, Fiori, and RISE
- Simulate access before provisioning to stop violations
- Analyze risk down to transaction codes and authorization objects
- Achieve faster ROI with automated SoD analysis
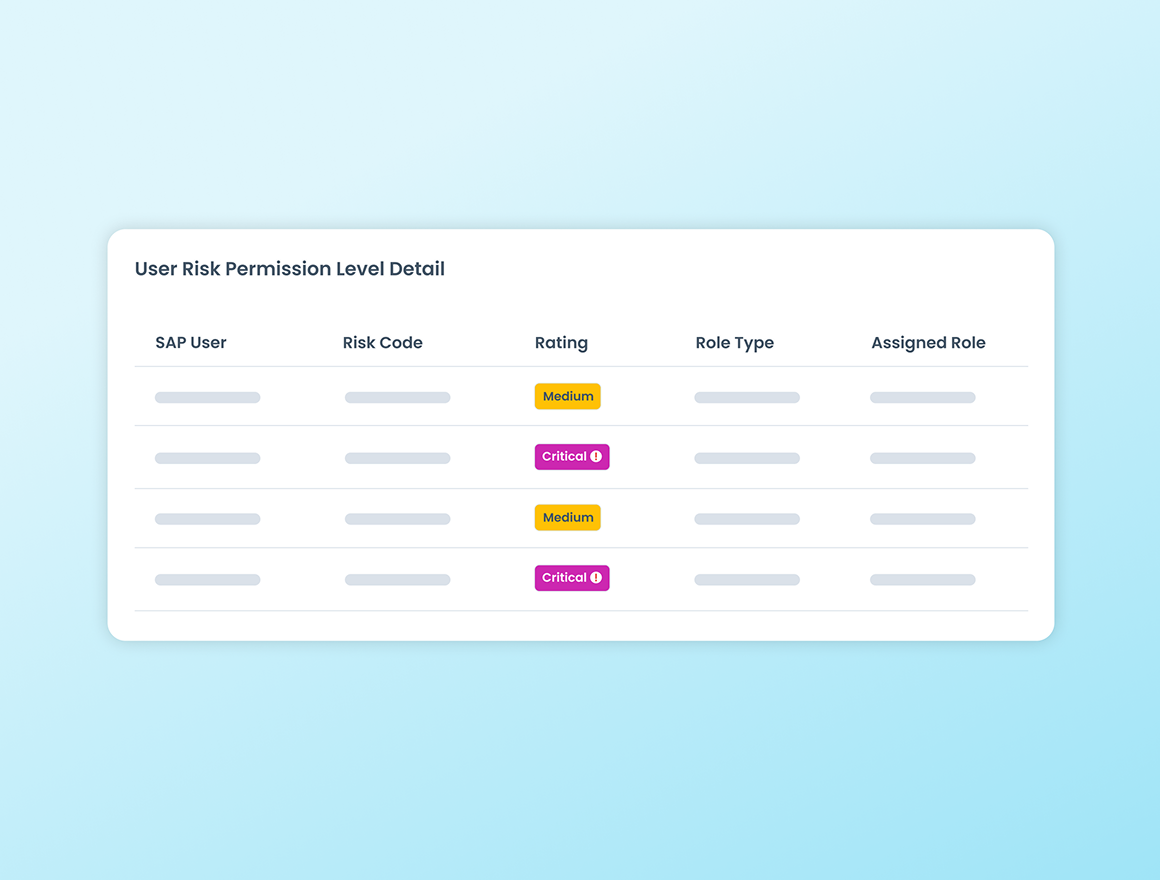
Detect and remediate high-risk access
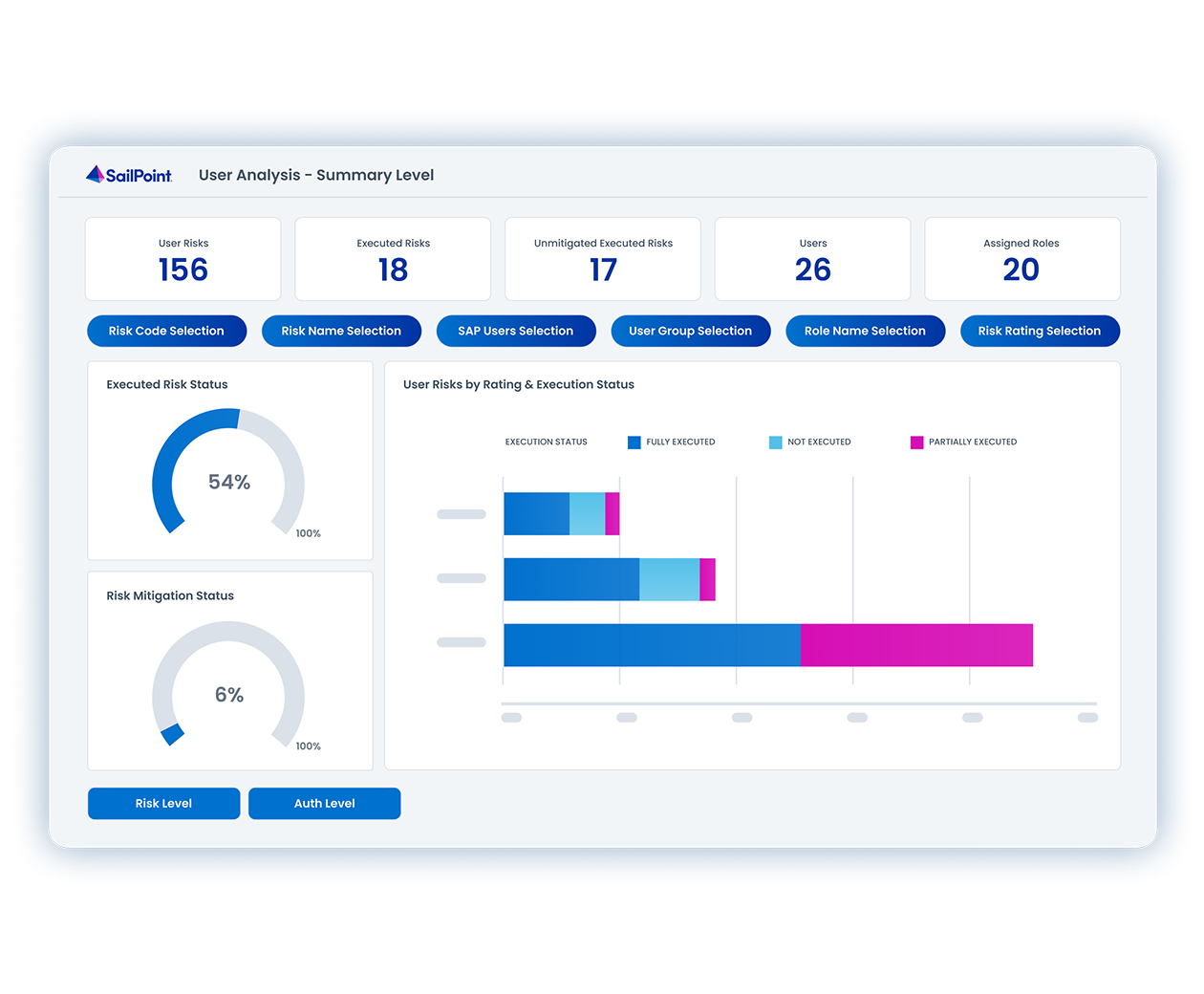
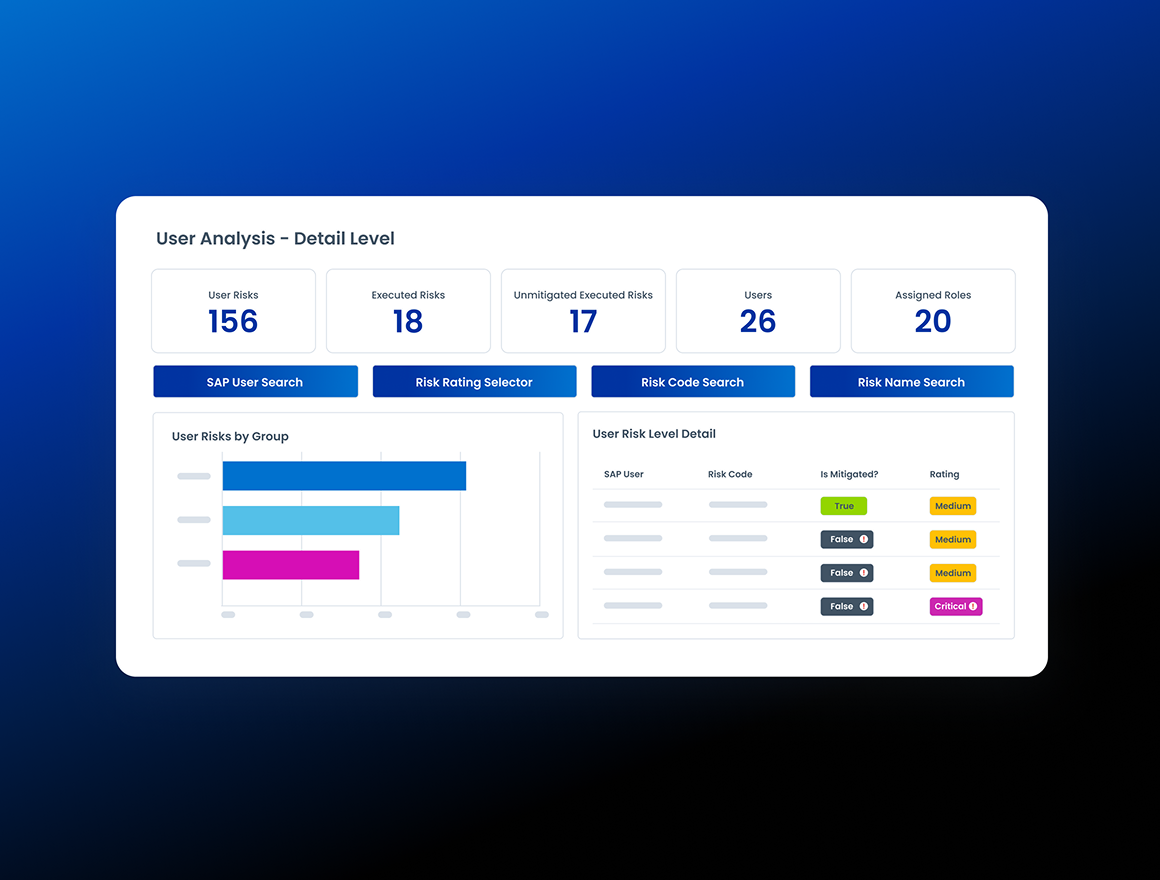
Automate risk analysis to find excessive or unused privileges. SailPoint Access Risk Management automatically flags violations, alerts security teams, and guides remediation to minimize exposure and insider threat risk.
- Proactively detect excessive, outdated, or unused access
- Automate alerts, mitigation, and emergency access workflows
- Visualize SAP risk exposure with intuitive dashboards
- Simplify audits with reports tailored to compliance needs
Unify SAP access governance
Manage SAP access risks alongside other enterprise systems within SailPoint’s Identity Security Cloud solution. Apply consistent policies, simplify certifications, and gain a single source of truth for access governance across all applications and data.
- Manage SAP and non-SAP access risks from a single platform
- Empower teams to act faster with data-driven insights
- Reduce audit fatigue and compliance overhead
- Apply consistent SoD and access policies

See SailPoint in action
Explore on your own
Take a self-guided tour of SailPoint's identity security platform
Take product tourRelated resources
Dig deeper into Access Risk Management
Start your identity security journey today
SailPoint Identity Security Cloud empowers organizations to intelligently manage and secure real-time access to critical data and applications.
Advanced capabilities
Take your identity security solution even further
SailPoint Identity Security Cloud goes beyond the basics to tackle complex identity challenges. These specialized, add-on solutions offer even greater control and intelligence for reducing risk and ensuring compliance.
INDUSTRY INSIGHTS
Control SAP access with confidence
SailPoint Access Risk Management helps organizations across industries reduce SoD conflicts, enforce compliant SAP access, and gain real-time visibility into high-risk user activities to protect critical systems and data.
Manufacturing
Monitor and prevent SoD conflicts across SAP production, procurement, and supply chain systems to keep operations compliant and running without interruption.
Learn moreHealthcare
Protect sensitive patient and financial data by automating SoD checks and access reviews to meet strict healthcare compliance standards.
Learn moreGovernment
Enforce policy-based SAP access controls and continuously detect SoD violations to strengthen accountability and transparency in government operations.
Learn morefaq
Frequently asked questions
What is SailPoint Access Risk Management?
SailPoint Access Risk Management is a cloud solution that helps organizations detect, monitor, and remediate SAP access risks and enforce SoD compliance, including Emergency Access Management.
How does Access Risk Management differ from SAP GRC Access Control?
SailPoint Access Risk Management delivers a fast, low-friction path to comprehensive access risk visibility with an enterprise-wide view, intuitive dashboards, and one-step reporting. With no heavy implementations, upgrades, or infrastructure costs, organizations get rapid time-to-value and low total cost of ownership. Automated reporting, streamlined reviews, and agile change management eliminate manual effort while reducing audit and consulting expenses.
What are segregation-of-duties (SoD) risks?
SoD risks occur when users have conflicting SAP access that could enable fraud. Access Risk Management detects and prevents these conflicts automatically.
Can Access Risk Management integrate with identity security solutions?
Yes. SailPoint Access Risk Management natively integrates with SailPoint Identity Security Cloud to unify SAP access controls and governance.
How does Access Risk Management support audits and compliance?
SailPoint Access Risk Management simplifies audits with automated SAP access reports, evidence collection, and SoD insights for SOX, GDPR, and HIPAA compliance.
How does Access Risk Management reduce manual SAP access tasks?
SailPoint Access Risk Management automates risk analysis, role design, and SoD remediation, reducing manual SAP reviews and improving compliance efficiency.
How quickly can organizations deploy SailPoint Access Risk Management?
SailPoint Access Risk Management’s SaaS deployment allows fast setup in weeks, with prebuilt rulebooks and automated onboarding enabling rapid risk mitigation.
How do organizations get started with SailPoint Access Risk Management?
Organizations can begin with Access Risk Management independently or choose the Access Risk Management QuickStart. This pre-packaged engagement accelerates deployment by focusing on key deliverables like configuring baseline policies and training your team. It ensures your access risk, SoD, and compliance use cases are addressed efficiently, delivering faster time to value.
Contact us
Put identity security at the core of securing your business


