Feb 20
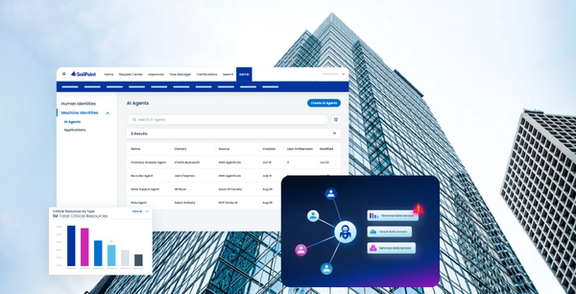
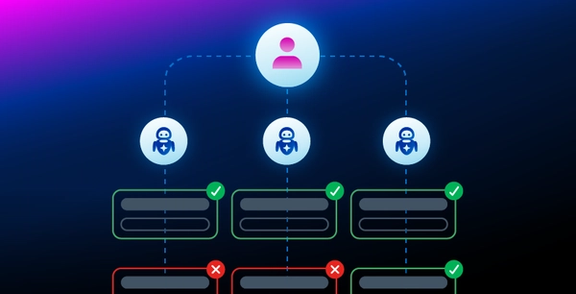
Introducing SailPoint’s new framework: Governing AI agents before they run wild
Discover how SailPoint's new AI governance framework helps enterprises manage the rapid rise of AI agents. Learn h...Discover how SailPoint's new AI governance framework helps enterprises manage the rapid rise of AI agents. Learn how to secure non-human identities, enforce access controls, and mitigate risks to scale AI safely and effectively.
Read blog