Cyber risk management, also referred to as cybersecurity risk management, is a continuous process of identifying, analyzing, prioritizing, managing, and monitoring digital assets to reduce risk and protect sensitive systems from cybersecurity threats. A part of all IT and business operations, cyber risk management is a critical function for all types of organizations.
As risks continue to grow and evolve, the enterprise is taking a holistic approach to cyber risk management.
This approach ensures that organizations have a comprehensive, consistent program that supports compliance efforts and increases overall cybersecurity.
When it comes to cyber risk management, don’t ignore a root cause of cyber risk. See how to protect digital identities.
The cyber risk management process
A cyber risk management process should begin by enabling all stakeholders to be part of the process. This ensures that the plan is truly holistic.
Beyond this, most cyber risk management processes include the following:
- Risk framing defines the context in which risk decisions are made.
- Risk assessment determines exposure, the likelihood of exploitation, and potential impact.
- Risk response includes plans for and prioritization of remediation.
- Risk monitoring plans provide guidance on how continuous monitoring controls will be implemented.
Why cyber risk management is important
Cyber risk management is important because it gives the enterprise the information it needs to proactively implement cybersecurity protections, mitigate vulnerabilities, and respond to threats. Because it is a cross-organizational effort, it raises awareness of what risks threaten the organization and the roles individuals play in neutralizing and responding to them. Also, the structure and processes that accompany cyber risk management give individuals the tools they need to become active participants in the organization’s efforts.
At a deeper level, cyber risk management brings more operational perspective to security groups. With the information teased out by these programs, analysts have more context for the threats they are seeking out and addressing and a new lens to use when considering cyber threats.
Cyber risk management is also important for organizations because it provides a structure and program for identifying, analyzing, prioritizing, managing, and monitoring cyber threats, including:
- Compromised credentials
- Dark web activity
- Malicious insiders
- Malware
- Ransomware
- Sensitive data leakage
- Third-party risks
A wide range of benefits are attributed to implementing cyber risk management:
- Proactive identification of vulnerabilities
- Mapping and monitoring of evolving attack surfaces for vulnerabilities leading to reduced attack surfaces
- Focused resources on threats likely to target high-value, critical assets
- Effective responses to evolving threats
- Improved compliance with regulations such as:
- Expedited business continuity with at-the-ready backups and incident response plans
- Enhanced understanding of risk across the enterprise
- Improved cybersecurity posture
- Better data security
- Bolstered trust and confidence in security and privacy protections
- General Data Protection Regulation (GDPR)
- Health Insurance Portability and Accountability Act (HIPAA)
- Payment Card Industry Data Security Standard (PCI-DSS)
Developing a cyber risk management plan
A cyber risk management plan has four core components.
- Identify cybersecurity risk (i.e., unplanned, negative outcome related to threats to IT systems). This phase includes the discovery and mapping of all digital assets to quantify the attack surface; the map is utilized as a foundation to monitor cybercriminal activity.
- Assess cyber risks.
This is comprised of the following core steps: - Implement cyber risk mitigation tactics.
Determine the appropriate tactics based on priorities and develop a plan to apply them to risks as applicable. - Monitor risks on an ongoing basis.
Once risks have been identified, create plans for continuous monitoring.
- Inventory all assets.
- Quantify the importance of each asset and create a list based on the priority.
- Evaluate threats to assets.
- Identify assets’ vulnerabilities.
- Determine the likelihood of a threat occurring.
Cyber risk management frameworks
A number of cyber risk management frameworks are available. Several were created for government agencies and others by organizations that made them available to the public. Some organizations are required to follow one or more of these frameworks, while others use them to develop their own guidelines.
Regardless of how or why they are used, any organization can benefit from the proven systems and methodologies set forth in the following cyber risk management frameworks.
NIST Risk Management Framework
The National Institute of Standards and Technology (NIST) Risk Management Framework (RMF) provides a comprehensive, flexible, repeatable, and measurable model for cyber risk management, including information security and privacy risk. It integrates security, privacy, and cyber supply chain risk management activities into the system development life cycle and incorporates new and legacy systems and technology, ranging from industrial control systems (ICS) to Internet of Things (IoT) devices.
The guidance provided in the NIST RMF is applicable to any type of organization, regardless of size or sector, and can be used to help organizations identify, eliminate, and minimize risks with systems implementations.
The NIST RMF is based on the seven-step process outlined below.
| Step | Description |
|---|---|
| Prepare | Details essential activities to prepare an organization to manage security and privacy risks. |
| Categorize | Directs how to categorize the system and information processed, stored, and transmitted based on an impact analysis. |
| Select | Helps with the selection of the set of NIST SP 800-53 controls needed to protect the system based on the risk assessment. |
| Implement | Provides guidance on the implementation of controls and how to document the way in which controls are deployed. |
| Assess | Guides assessments to determine if the controls are in place, operating as intended, and producing the desired results. |
| Authorize | Directs a senior official to make a risk-based decision to authorize the system to go into production. |
| Monitor | Guides the continuous monitoring of controls implementation and status of risks, known and new, to the system. |
NIST Special Publication 800-30
NIST Special Publication 800-30 is titled the Guide for Conducting Risk Assessments. NIST SP 800-30 is used to conduct risk assessments and translate cyber risk in a way that can be understood by business leaders (e.g., executive team and board of directors).
NIST SP 800-30 supports cyber risk management initiatives by providing a common language between technical and business leadership that facilitates alignment and helps them make informed decisions about resource allocation based on threat types, operational impact, and financial impact. This information is based on a baseline risk assessment that assesses the current standard of operation within the system, flags potential security issues, and directs remediation.
NIST Cybersecurity Framework
The NIST Cybersecurity Framework (NIST CSF) provides a comprehensive set of best practices that standardize cyber risk management. It details recommended functions and outcomes related to the core functions of cyber risk management—protect, detect, identify, respond, and recover. This framework is designed to help organizations better manage and reduce cyber risk of all types (e.g., malware, password compromise, social engineering attacks, distributed denial-of-service (DDoS) attacks, traffic interception, and ransomware).
Among the directives related to cyber risk management, the NIST CSF states that “the organization understands the cybersecurity risk to organizational operations (including mission, function, image, or reputation), organizational assets, and individuals.” It further states that the organization’s priorities, constraints, risk tolerances, and assumptions need to be established to support operational risk decisions.”
The NIST CSF recommends organizations take specific steps to reduce risk, including:
- Analyze threats, vulnerabilities, likelihood, and impacts to prioritize risks and responses.
- Identify and document asset vulnerabilities.
- Identify and document internal and external risks, their potential business impacts, and the likelihood of risk events.
- Leverage cyber threat intelligence from information-sharing forums.
NIST CSF also has a section detailing what needs to be included within a risk management strategy, stating that “the organization’s priorities, constraints, risk tolerances, and assumptions need to be established to support operational risk decisions.” Further, the framework asks organizations to establish and implement processes to identify, assess, and manage supply chain risks.
ISO/IEC 27001
The International Organization for Standardization (ISO) created the ISO/IEC 27001 in partnership with the International Electrotechnical Commission (IEC). This framework provides a set of standards for systematically managing risks related to information systems. Standards related to cyber risk management say that organizations must:
- Analyze and evaluate information security risks continuously.
- Ensure that repeated risk assessments produce consistent, valid, and comparable results.
- Establish and maintain information security risk criteria.
- Identify risks associated with the loss of confidentiality, integrity, and availability (i.e., the CIA triad) for information within the scope of an information security management system.
- Identify those responsible for identified risks and related stakeholders.
Department of Defense Risk Management Framework
This risk management framework (RMF) defines cyber risk management guidelines for Department of Defense (DoD) agencies to use when assessing and managing cybersecurity risks. According to the DoD RMF, a cyber risk management strategy should be based on seven key steps:
- Prepare.
- Categorize information systems.
- Select security controls.
- Implement security controls.
- Assess security controls.
- Authorize the information system.
- Monitor security controls.
Factor Analysis of Information Risk
The Factor Analysis of Information Risk (FAIR) framework was developed to help enterprises measure, analyze, and understand information risks. This quantitative and probabilistic model for cyber risk management and analysis breaks down cyber risk into two components—loss event frequency and loss magnitude. It then weighs threat capability, vulnerability, resistance strength, and loss types to calculate the risk and impact of cyber incidents.
Operationally Critical Threat, Asset, and Vulnerability Evaluation
The Operationally Critical Threat, Asset, and Vulnerability Evaluation (OCTAVE) was developed by the Software Engineering Institute at Carnegie Mellon University as a self-directed and collaborative approach for cyber risk assessment, planning, and mitigation. The OCTAVE method involves three top-level phases:
- Establishing drivers and objectives
- Identifying critical assets and threats
- Developing mitigation plans and strategies
The OCTAVE method can help organizations understand their risk profile, assets, and dependencies and design solutions that address specific needs and goals.
There are two sub-versions for specific organization types—OCTAVE Allegro and OCTAVE FORTE. OCTAVE FORTE (OCTAVE FOR the enterprise) has ten steps for cyber risk management:
- Establish risk governance and appetite.
- Scope critical services and assets.
- Identify resilience requirements of assets.
- Measure current capabilities.
- Identify risks, threats, and vulnerabilities to assets.
- Analyze risks against capabilities.
- Plan for response.
- Implement the response plan.
- Monitor and measure for effectiveness.
- Review, update, and repeat.
OCTAVE Allegro (for small and mid-sized businesses) is comprised of eight steps for cyber risk management:
- Establish risk measurement and criteria.
- Develop an information asset profile.
- Identify information asset containers.
- Identify areas of concern.
- Identify threat scenarios.
- Identify risks.
- Analyze risks.
- Select response approaches.
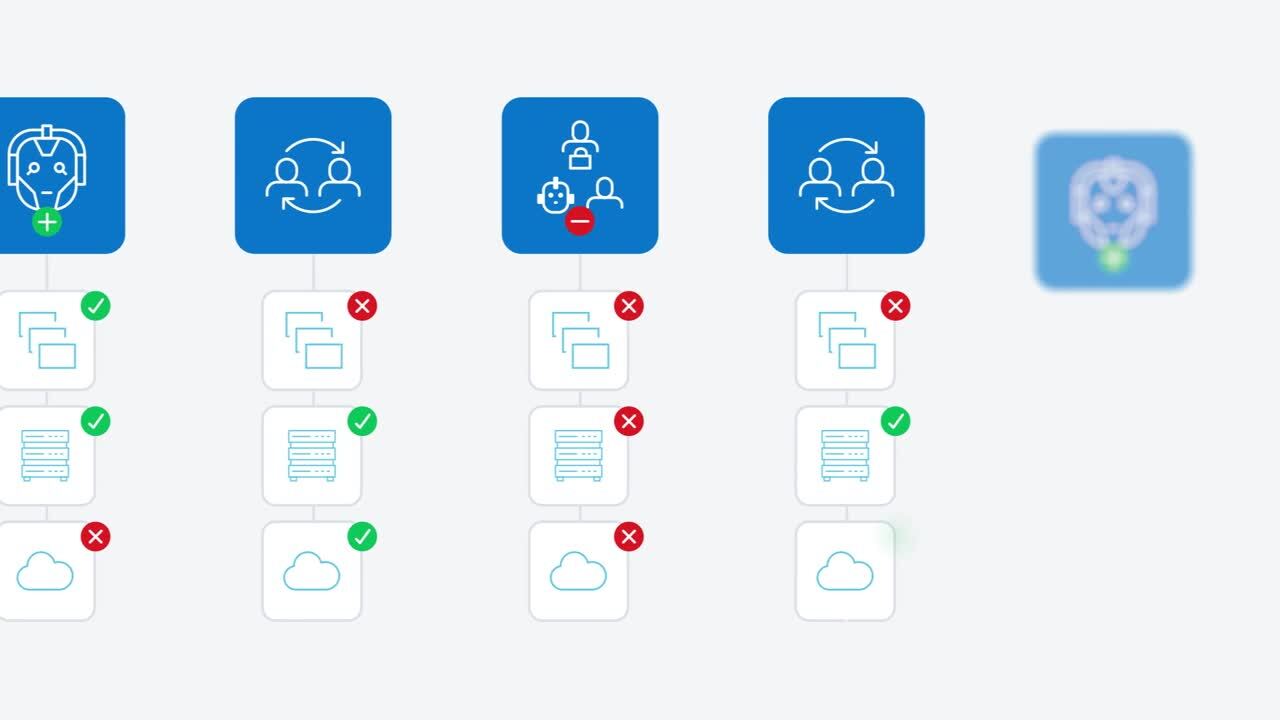
Cyber risk management roles
There are a number of roles involved in cyber risk management, though many are peripheral. Cyber risk management roles in organizations may include the following.
Chief Information Security Officer (CISO)
The CISO oversees the organization’s overall cybersecurity strategy. As part of this, CISOs are accountable for managing cyber risks.
To support cyber risk management initiatives, CISOs work closely with other executives to ensure that cybersecurity programs and processes align with and meet the requirements for business operations functions as well as the organization’s risk tolerance. Other cyber risk management functions that CISOs oversee include:
- Balancing the need for security with the organization’s operational requirements
- Communicating key messages related to security, risks, and incidents to technical and non-technical stakeholders
- Identifying, assessing, and prioritizing security risks
- Overseeing the assessment and management of cybersecurity risks associated with third-party relationships
Cyber Risk Responsible Executive (CRE)
The CRE is an individual in senior management who is accountable for cyber risk management, including risk assessments, analysis, mitigation, and monitoring. In larger organizations, the CRE is a chief risk officer (CRO). The CRE is also responsible for helping the organization determine risk acceptance levels and overseeing the implementation of cyber risk management programs to support them.
Cyber Risk Analyst
A cyber risk analyst, sometimes referred to as a cyber risk coordinator, is responsible for:
- Aligning cybersecurity processes and controls to the relevant frameworks and internal systems
- Analyzing potential business and customer risk
- Conducting security assessments and policy reviews
- Creating cyber risk analysis reports
- Evaluating the organization’s level of cyber risk
- Identifying, assessing, and consulting on areas of cybersecurity risk to resolve or mitigate risks
- Informing decisions about risk mitigation and risk acceptance
- Oversee the operational side of threat detection
- Supporting cyber risk analysis, classification, and response across the organization
Cybersecurity Program Manager
Among the many responsibilities of cybersecurity program managers is to ensure that cybersecurity projects align with the organization’s cyber risk management strategy.
Security Awareness and Training Specialist
A security awareness and training specialist focuses on programming to ensure that all users understand the risks that the organization faces and the security protocols that mitigate them. They provide information and conduct training to ensure that all users have the understanding, training, and resources needed to support the organization’s overarching cyber risk management program effectively.
Third-Party Risk Manager
Vendor risk managers assess and manage the cybersecurity risks associated with external relationships (e.g., partners, vendors, and customers). They help develop acceptable risk criteria and ensure that third parties meet these standards through initial assessments and regular audits.
Cyber risk management best practices and key capabilities
Effective cyber risk management programs offer a number of best practices and include supporting capabilities, including:
- Defining roles and specific responsibilities
- Developing robust policies and tools to assess vendor risk
- Identifying emergent risks, such as changing regulations and evolving threat vectors
- Identify and assess the efficacy of security controls and other mitigation measures
- Test security controls regularly
- Leverage cyber risk management frameworks
Tools that support cyber risk management efforts are those that support:
- Analytics
- Auditing
- Collaboration and communication
- Data management
- Issue management and tracking
- Reporting
- Workflow optimization
Cyber risk management bolsters cybersecurity across the enterprise
The value of cyber risk management to cybersecurity is clear to many technical and business executives. These initiatives drive security awareness into the consciousness of management and staff across organizations as well as into programs that enhance overall security. As the threat landscape continues to evolve and spawn more virulent attacks, cyber risk management expands the reach of cybersecurity through awareness and engagement.
Cyber risk management not only improves cybersecurity but helps organizations address a dizzying array of regulations. Many of these come with strict requirements for data security and privacy controls. In addition to raising awareness and increasing the efficacy of cybersecurity, cyber risk management provides the auditing and reporting elements required by many regulations.
Although cybersecurity threats and vulnerabilities cannot be completely eliminated, cyber risk management can help organizations identify and address many of them. Cyber risk management benefits all organizations as they continue to expand the depth and breadth of their programs.