Use case
Automate trust across the lifecycle
From onboarding to revalidation, verify every non-employee identity with accuracy and control.

Challenge & solution
Ensure every identity is trusted
Confirm who non-employees are before access is granted—and revalidate them as relationships change. Enforce credential checks, prevent duplicates, and maintain trust throughout each assignment.
Lack of oversight fuels identity risk
Inconsistent verification across vendors, contractors, and partners leaves gaps in oversight
Enrich access reviews with sensitivity and usage metadata
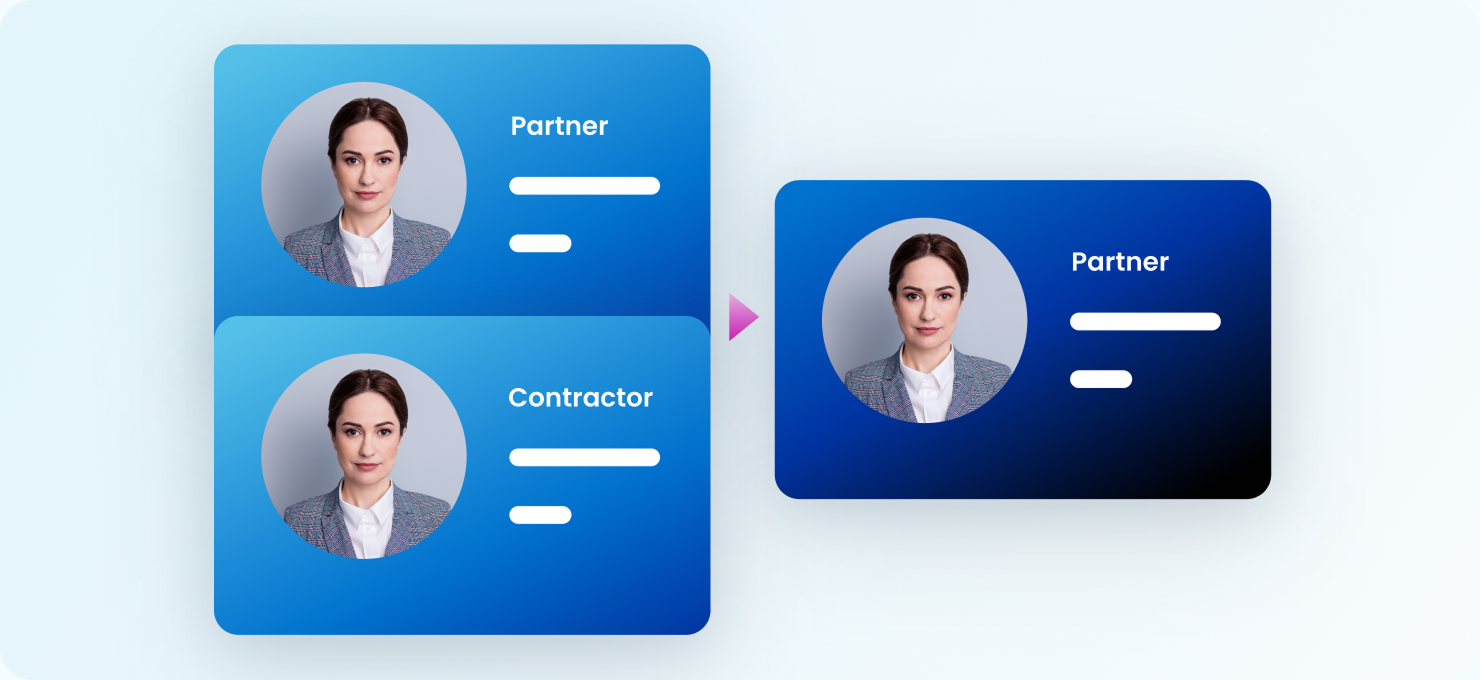
Duplicate identities create confusion over ownership and proper access levels
Long-term assignments rarely get revalidated, allowing outdated access to persist unchecked
Ensure accuracy, compliance, and control
Automate identity proofing and credential validation to confirm each individual before access is granted
Enforce policy-based onboarding requirements like training, NDAs, and background checks through guided workflows
Maintain accurate, unified records for each non-employee to prevent duplicate or inherited accounts
Schedule periodic reverification for high-risk or long-term roles to sustain oversight and help ensure continued compliance
FAQ
Technical insight and guidance
Learn how to effectively manage and secure your extended workforce with insights on verification, revalidation, and more.
Benefits
Automate trust across the lifecycle
Verification starts at onboarding, but maintaining trust requires ongoing oversight. By verifying non-employees and third parties before access is granted—and revalidating them as projects, roles, or relationships change—organisations can ensure that only the right people have the right access at every stage. This unified approach strengthens compliance and reduces identity-related risk.
Secure access from the start
Validate each non-employee’s identity and credentials during onboarding. Integrate with trusted verification providers and enforce prerequisites—like NDAs, training, or background checks—so only verified, qualified individuals gain access on day one.
Advanced capabilities
Take your identity security solution even further
SailPoint defines the future of adaptive identity for the AI-driven enterprise. Our comprehensive vision and AI-powered platform empower you to secure every identity—human and non-human—transforming risk into a powerful advantage and enabling confident AI innovation.
Related industries
Verification and oversight across industries
Every industry faces unique challenges managing non-employee access. From credential verification to ongoing revalidation, Non-Employee Risk Management adapts to each sector’s needs—helping ensure every identity stays accurate, compliant, and secure.
Healthcare
Verify and track rotating staff—like travel nurses or affiliate physicians—to help ensure credentials stay current, and access remains secure.
Learn moreFinancial services
Revalidate third-party access to sensitive systems to reduce risk and help maintain regulatory compliance.
Explore financeEducation
Proof and revalidate access for adjunct faculty, researchers, and visiting scholars to help ensure accountability and security.
Explore educationfaq
Answers about verification & trust
What is the difference between verification and revalidation?
Verification happens during onboarding—it confirms a non-employee’s identity and required credentials before access is granted. Revalidation happens later, ensuring that identities are still active with your organisation and still require access. Together, they help create a closed loop of trust that extends across the entire non-employee lifecycle.
How does Non-Employee Risk Management perform identity proofing?
The solution integrates with trusted verification providers to confirm each individual’s identity and credentials at onboarding. It can also enforce completion of training, NDAs, or background checks before access is approved. These automated checks replace manual review processes, helping organisations onboard quickly without sacrificing security.
Can organisations configure their own verification requirements?
Yes. Administrators can define pre-access requirements such as digital credentials, attestations, or policy acknowledgments, and tie them to specific role types or risk levels. This flexibility allows each organisation to maintain governance standards while adapting verification steps to the unique needs of different business units or partner types.
How are duplicate or inherited accounts prevented?
During onboarding, the system detects potential duplicate records based on configurable attributes, such as name, email, or vendor association. It then flags these for review or merges them, ensuring each non-employee maintains a single, accurate identity record. This prevents confusion, misattribution, and unnecessary risk exposure.
How does revalidation work for long-term or high-risk non-employees?
By providing visibility into data access, sensitivity, and usage, SailPoint helps organisations create a more efficient, transparent certification process that aligns with internal controls and regulatory expectations.
How does the solution support audits and compliance reporting?
Every verification, credential check, assignment change, and revalidation is automatically logged with time-stamped details. This creates a transparent, end-to-end record of identity activity across all non-employees. During audits, teams can quickly produce evidence that shows who was verified, when revalidation occurred, and what access was provided—reducing the manual effort typically required to prove compliance.
contact us
Secure and govern sensitive data access
Discover how SailPoint can help you reduce risk, enforce least privilege, and protect sensitive data with identity-first governance.