Data model
Gain fast access to insights & identity context
At the core of SailPoint Atlas is a unified, extensible data model connecting identities, access, policies, and risk signals. It creates a single source of identity truth, powering AI-driven insight, automation, faster decisions, and precise policy enforcement at scale.
Challenge & solution
Solving identity data challenges
Organisations struggle with fragmented identity data, siloed systems, and inconsistent governance, making it difficult to manage identities, entitlements, and risks effectively. Without a unified data model, they face challenges in automating workflows, detecting anomalies, and ensuring precise, scalable security. These gaps hinder visibility, slow decision-making, and limit the ability to adapt to evolving business and security needs.
Powering AI-driven insights and automation
Unifies identity data into a single, trusted source for consistent governance and decision-making.
Eliminates data silos, enabling seamless integration across identity and security programs.
Powers AI to detect anomalies, recommend access, and automate certifications with precision.
Powers visibility within the identity graph for clear access paths and risk insights.
Enables dynamic workflows that adapt to identity posture, risk, and business context changes.
Use Cases
Empowering smarter, adaptive identity security
Discover how SailPoint’s unified data model powers identity intelligence, dynamic workflow automation, and real-time visibility—enabling smarter decisions, adaptive security, and seamless governance.

Unified identity intelligence
The SailPoint data model centralises identity, entitlement, and risk data into a single source of truth. This unified foundation eliminates silos, enabling AI to analyse behaviour, detect anomalies, and recommend smarter access decisions. Organisations gain consistent, context-rich insights to streamline governance, enhance security, and drive automation.
Dynamic workflow automation
With a consistent understanding of identity relationships, the data model powers intelligent workflows. It enables real-time responses to identity posture changes, such as escalating access requests or triggering remediation. By integrating with external security systems, it ensures precise, automated actions that adapt to evolving risks and business contexts.

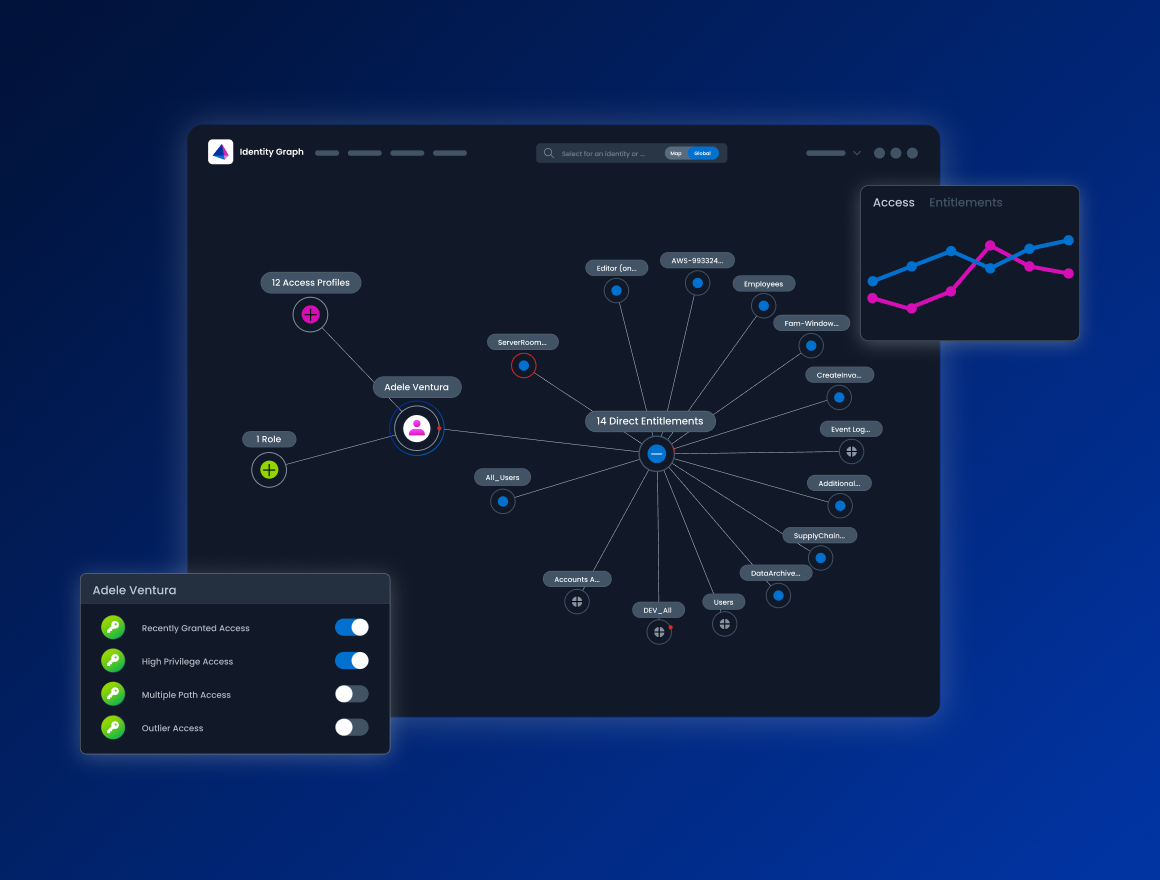
Real-time identity visibility
The data model fuels the Observability and Insights advanced capability, providing a interactive graph of identities, entitlements, and access paths. This clarity helps organisations see who has access to what, identify hidden risks, and track access changes over time. It delivers actionable insights for audits, compliance, and security operations, ensuring informed, strategic decision-making.
Our Customers
The world’s leading enterprises trust SailPoint
53% of the Fortune 500 and 28% of the Forbes Global 2000










See SailPoint in action
Explore on your own
Take a self-guided tour of SailPoint's identity security platform
Self-guided demoStart your identity security journey today
SailPoint Identity Security Cloud empowers organizations to intelligently manage and secure real-time access to critical data and applications.
Advanced capabilities
Take your identity security solution even further
SailPoint defines the future of adaptive identity for the AI-driven enterprise. Our comprehensive vision and AI-powered platform empower you to secure every identity—human and non-human—transforming risk into a powerful advantage and enabling confident AI innovation.
FAQ
Frequently Asked Questions
How does the data model enhance security?
By providing a centralised and normalised view of identity data, the model empowers AI to continuously analyse behaviour, detect anomalies, and recommend least-privilege access. It ensures that governance policies are applied with precision, reducing risks and enabling organisations to respond quickly to potential threats while maintaining operational efficiency.
What role does AI play in the SailPoint data model?
AI is deeply integrated into the data model, leveraging its unified foundation to analyse identity behaviour, detect outliers, and recommend smarter access decisions. It automates complex tasks like role design, access certifications, and anomaly detection, enabling organisations to operate with greater precision and confidence while reducing manual effort.
How does the data model support workflow automation?
The data model powers intelligent workflows by providing a consistent understanding of identity relationships and events. This enables dynamic automation, such as escalating or auto-approving access requests based on real-time signals, triggering remediation for anomalous activity, and coordinating actions across security tools through the Shared Signals Framework.
What is the identity graph, and how does it help?
The SailPoint Observability and Insights advanced capability provides an interactive identity graph which maps identities, entitlements, and access paths and is built using the SailPoint data model. It transforms fragmented identity data into a connected, contextual foundation, offering unmatched clarity into who has access to what, identifying hidden risks, and tracking how access changes over time. This visibility is critical for audits, compliance, and proactive risk management.
How does the data model improve visibility?
By normalising data from various sources—such as HR systems, cloud platforms, and applications—the data model creates a comprehensive, real-time view of identity relationships. This clarity helps organisations identify risks, assess the impact of potential threats, and make informed decisions to strengthen security and governance. The data model enables multiple forms of data visualisation and reporting capabilities to ensure easy, secure and comprehensive insights.
What are the benefits of the Access Intelligence Center (AIC)?
The AIC leverages the data model to unify identity, access, and activity data into a single, consistent source of truth. It provides granular, real-time analytics through dashboards and reports, helping organisations monitor compliance, identify anomalies, and measure the maturity of their identity programs. This actionable intelligence enables faster, more strategic decision-making.
How does the data model ensure a unified SailPoint experience?
The data model serves as the backbone for all SailPoint products, centralising identity, access, and risk data into a single, trusted framework. This shared foundation allows engineering teams to collaborate seamlessly, innovate faster, and deliver cohesive capabilities across the SailPoint ecosystem. Customers benefit from a consistent, integrated experience that enhances usability and interoperability.
Contact us
Put identity security at the core of securing your business





