Observability & insights
Clearly see every identity
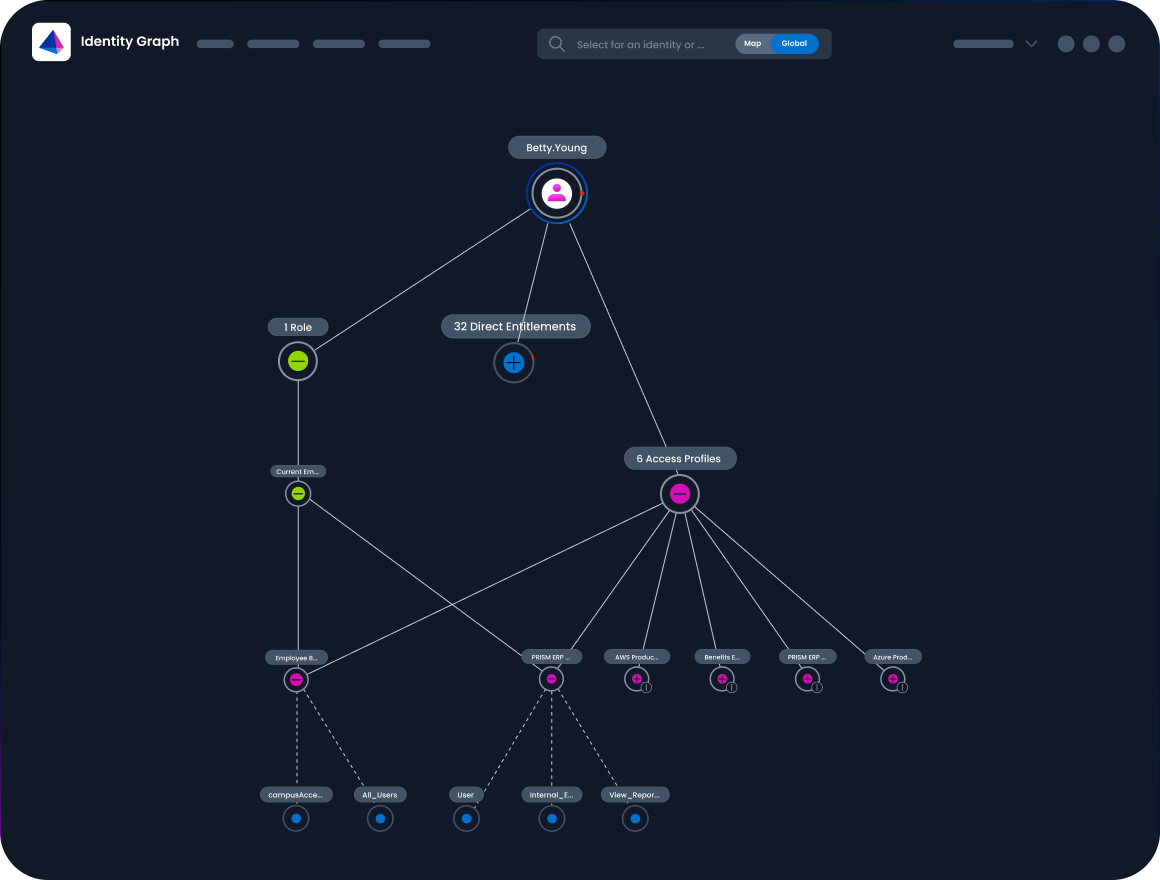
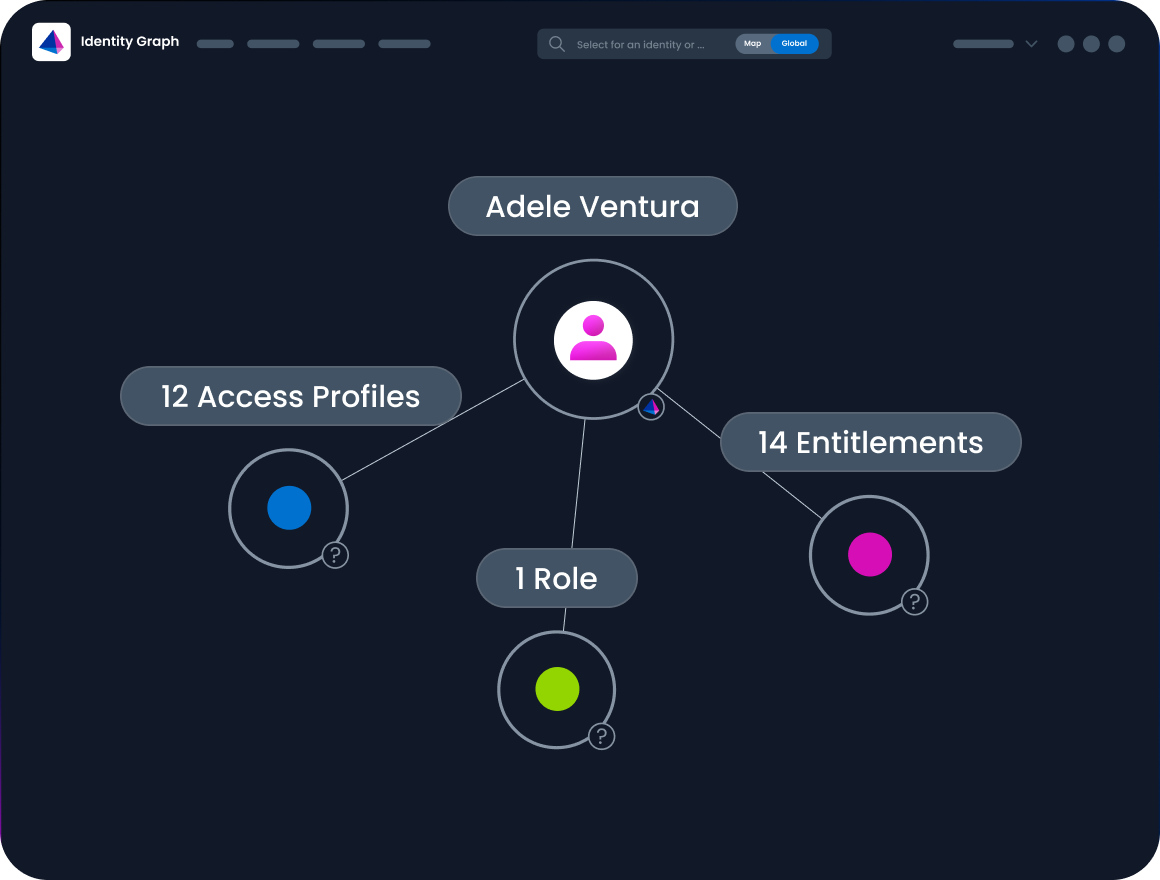
See your entire identity landscape with clarity. Transform fragmented data into actionable context with an interactive identity graph.
Proactively manage identity risk. Uncover and address risky entitlements with rich context and intuitive filtering to enforce least privilege access.
Streamline governance and response. Visualize the impact of a breach with blast radius analysis and risk heatmaps to prioritize and accelerate your response.
Get live demo
Trusted by 51% of the Fortune 500
How we help
See how SailPoint turns identity blind spots into actionable insights.
Identity is now the dominant attack vector, and blind spots are no longer acceptable. Disconnected systems and hidden entitlements make confident access governance nearly impossible, leaving organizations exposed. Visual maps of identities, entitlements, and access paths give leaders full environment clarity. Risk heatmaps and rare-access detection surface the anomalies that matter most—strengthening governance and supporting zero-trust maturity.
IAM teams are often buried in spreadsheets, disconnected logs, and nonstop access review requests. Even basic questions—like who can access a sensitive system—can require hours of manual work. An intuitive identity graph replaces that complexity with clarity, showing direct and inherited access in one view. Redundant entitlements become easier to remediate, reviews run faster, and continuous updates improve accuracy as users join, move, or leave.
When credentials are compromised, security teams need insight within minutes. But SOCs often can’t correlate identity data across siloed tools, delaying response. An identity graph shows every entitlement, role, and application a compromised identity reaches, while blast-radius analysis exposes potential impact. Shared IAM–SOC context improves coordination and helps reduce containment time, limit damage, and strengthen resilience.

OUR PARTNERS
Our global partner ecosystem
We partner with the many of the most innovative companies to provide identity security for the modern enterprise. Our partner ecosystem offers consulting, implementation, and services on SailPoint deployments, as well as integrations that help drive your business.
Explore our partnersOne platform to secure every identity
Adaptive identity security, powered in real time
Unify identity, data, and security intelligence in real time with the SailPoint platform. Continuously assess risk, context, and behavior across all identities—human and non-human—to dynamically adjust access, automate decisions, and enforce least privilege as business and threats evolve.
OUR CUSTOMERS
Many of the world’s leading enterprises trust SailPoint
50% of the Fortune 500 and 25% of the Forbes Global 2000



