A lot has changed since The 2019 Identity Report. At the time of the report’s publication, we shared our concerns that support for identity programs within most organizations were lacking. Many organizations lack maturity in how they govern identities; and data sprawl is overwhelming, unmonitored, and unmanaged.
As we look to 2020, the items we highlighted as areas of concern are now real-world problems for many companies. In the last few weeks, there has been an uptick in companies provisioning and securing existing workers for remote work, on-boarding new contingent workers to address new resourcing needs and pausing employment for those who are being furloughed.
As organizations attempt to successfully navigate this and future crises, they have realized that identity access and management is more than a nice to have. If anything, having a robust identity solution ensures the right people have the right access needed to do their jobs – and fast.
The Main Takeaway: Organizations need identity provisioning to ensure workforce continuity.
The State of Identity: Remote Working and Collaboration in the Digital Era
Identity governance enables and secures digital identities for all users, applications and data. It should be the center of an organization’s security and compliance strategy because it gives organizations the ability to answer three critical questions:
- Who has access to what?
- Who should have access?
- What are your users doing with their access?
When enterprises are able to answer all three questions, they are better protected against potential threats, and able to more efficiently manage and govern the users and resources that are part of daily business. The ultimate goal of any identity programis to efficiently deliver access to its users, securely and confidently.
To see where the gaps are in organizations’ identity programs today, SailPoint partnered with Identropy, an identity management and consulting firm, to create the Identity Score self-assessment. Leveraging their extensive expertise with identity governance implementations, SailPoint and Identropy first mapped what a comprehensive identity program is in today’s environment. Then, the two companies determined what an ideal implementation and maintenance processes look like and how the maturity and efficiency of these processes impact an organization’s risk of a data breach. The assessment also sought to determine the level of protection each enterprise had over its data – both those in structured systems such as SAP, Oracle or Workday, and data stored in file shares such as Dropbox and SharePoint.
Ensure the right people have the right access to do their jobs — and fast.
What is an Identity Score?
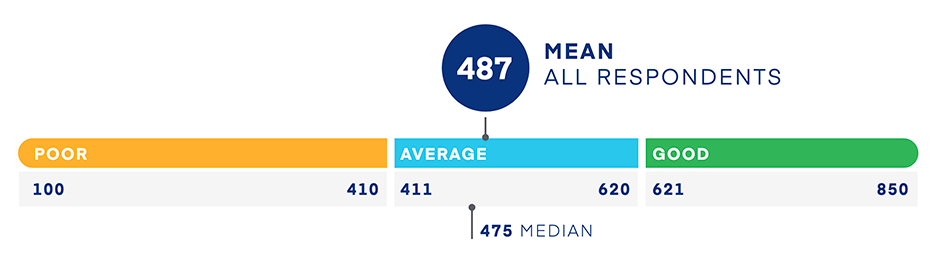
In 2019, to better understand the state of the identity preparedness globally, we surveyed more than 750 individuals that represent a variety of industries, organization sizes, and geographical locations. An identity score is based upon how survey respondents answered the Identity Score self-assessment, and then they were assigned ranges from 100 – 850, much like a credit score. Most organizations fell within the 411 – 620 range (Average), with a Good score rated above 620 and a Poor score rated under 411. It should be noted that half of all respondents scored in the expected range, Average, which means there is plenty of room for improvement in enterprise security.
Figure 1 | Mean Identity Score for All Respondents
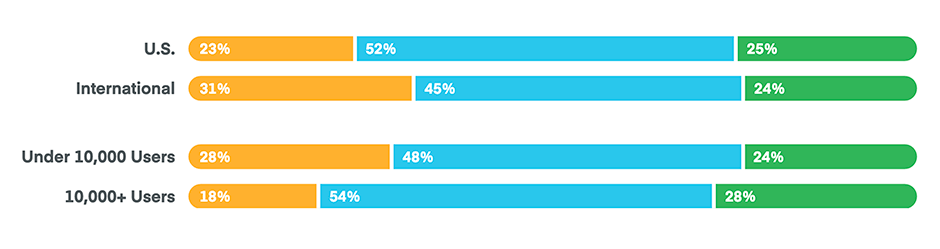
Unsurprisingly, larger enterprises scored better than their small- to mid-market counterparts, suggesting that more mature organizations have more mature identity programs. Additionally, international organizations had an overall lower percentage of “Average” and “Good” scores, though there were a similar number of Good scores, see below graph.
Figure 2 | Identity Processes Scores by Geography & Organization Size
The Top 4 Things Organizations Should Do Now
Given what we learned from the survey respondents, there are certain things every organization should do to both further mature their identity program and better secure corporate resources:
- Perform a full audit on identities’ access to systems, applications and data across the entire enterprise.
- Identify weak areas in visibility over users’ access to any corporate resource and determine the current status of the identity program today versus its ideal state.
- Don’t forget to determine the level of connectivity among each part of the security environment. Every system and resource should be connected to the organization’s identity governance solution.
- Ensure all the identity processes that can be automated, are.
- When users either join, move within or leave the company, access should be provisioned or deprovisioned immediately and checked against security policies to ensure only the minimum amount of access has been granted for their current role.
- Enable self-service when possible and appropriate given security policies for services including password resets and access requests.
- Build a channel for users to request the procurement of new applications, but don’t make it overly complicated.
- Get control over data.
- The first step is to find and classify all data within the enterprise. A tool that can discover data automatically in both structured and unstructured systems will be extremely beneficial.
- That same tool should also classify corporate data and score it in terms of risk, marking certain files or repositories as sensitive information.
- Elect owners for all data by selecting someone in a supervisory or project management role.
- Regularly review and alter, if necessary, each aspect of the identity program.
- This includes more than just setting certain processes like re-certification on a set schedule.
You might also be interested in:
Find out how we help you create your ideal identity program.
*required fields


