Trust No One Automatically when Giving Access to Cloud-based Assets
Conventional perimeter-based security models that relied solely on network location are now obsolete. In its place is Zero Trust — a security paradigm that aims to help organizations drive digital business with maximum security in their AWS Cloud without compromising efficiency or compliance.
Identity security is the cornerstone of an effective Zero Trust strategy. When evaluating identity security solutions for your AWS Cloud, look carefully at how they help you implement three essential requirements of an identity-aware Zero Trust security model.
- Never trust – always verify
- Deliver Just-in-Time (JIT) access
- Continuously monitor, analyze, and adapt
Fill out the form for access to the eBook.
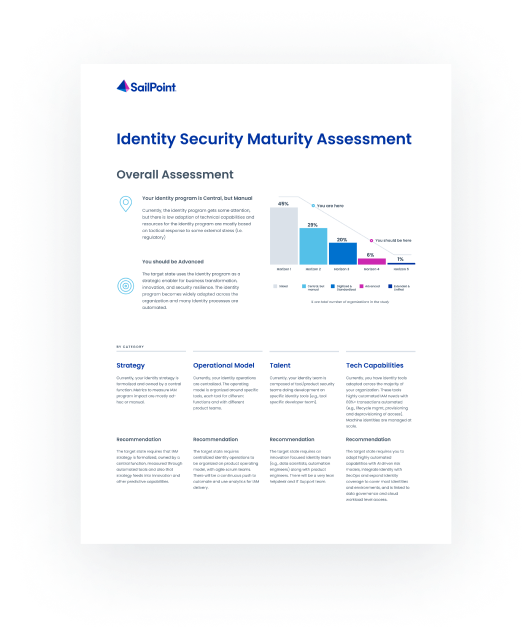
Take the assessment
Assess the maturity of your identity capabilities and identify the gaps to start your identity transformation!